Chapter: Embedded Systems Design : Embedded processors
8 bit accumulator processors
8 bit accumulator processors
This category of processor first appeared in the mid-1970s as the first
microprocessors. Devices such as the 8080 from Intel and the MC6800 from
Motorola started the microprocessor revolution. They provided about 1 MIP of
performance and were at their introduction the fastest processors available.
Register models
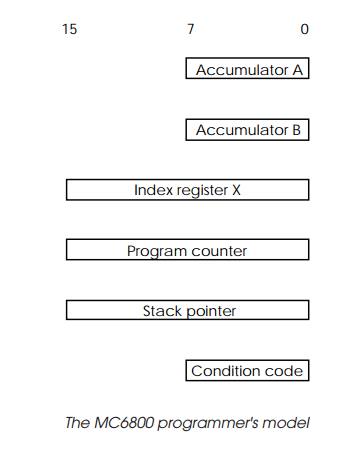
The programmer has a very simple register model for this type of
processor. The model for the Motorola MC6800 8 bit processor is shown as an
example but it is very representative of the many processors that appeared (and
subsequently vanished). It has two 8 bit accumulators used for storing data and
performing arithmetic operations. The program counter is 16 bits in size and
two further 16 bit registers are provided for stack manipulations and address
indexing.
On first inspection, the model seems quite primitive and not capable of
providing the basis of a computer system. There do not seem to be enough
registers to hold data, let alone manipulate it! Comparing this with the
register laden RISC architectures that feature today, this is a valid
conclusion. What is often forgotten is that many of the instructions, such as
logical operations, can operate on direct memory using the index register to
act as pointer. This removes the need to bring data into the processor at the
expense of extra memory cycles and the need for additional or wider registers.
The main area within memory that is used for data storage is known as the
stack. It is normally accessed using a special register that indexes into the
area called the stack pointer.
This is used to provide local data storage for programs and to store
information for the processor such as return addresses for subrou-tine jumps
and interrupts.
The stack pointer provides additional storage for the pro-grammer: it is
used to store data like return addresses for subrou-tine calls and provides
additional variable storage using a PUSH/ POP mechanism. Data is PUSHed onto
the stack to store it, and POPed off to retrieve it. Providing the programmer
can track where the data resides in these stack frames, it offers a good
replacement for the missing registers.
8 bit data restrictions
An 8 bit data value can provide an unsigned resolution of only 256 bits,
which makes it unsuitable for applications where a higher resolution is needed.
In these cases, such as financial, arithmetic, high precision servo control
systems, the obvious solution is to increase the data size to 16 bits. This
would give a resolution of 65536 — an obvious improvement. This may be acceptable
for a control system but is still not good enough for a data processing
program, where a 32 bit data value may have to be defined to provide sufficient
integer range. While there is no difficulty with storing 8, 16, 32 or even 64
bits in external memory, even though this requires multiple bus accesses, it
does prevent the direct manipulation of data through the instruction set.
However, due to the register model, data larger than 8 bits cannot use
the standard arithmetic instructions applicable to 8 bit data stored in the
accumulator. This means that even a simple 16 bit addition or multiplication
has to be carried out as a series of instructions using the 8 bit model. This
reduces the overall effi-ciency of the architecture.
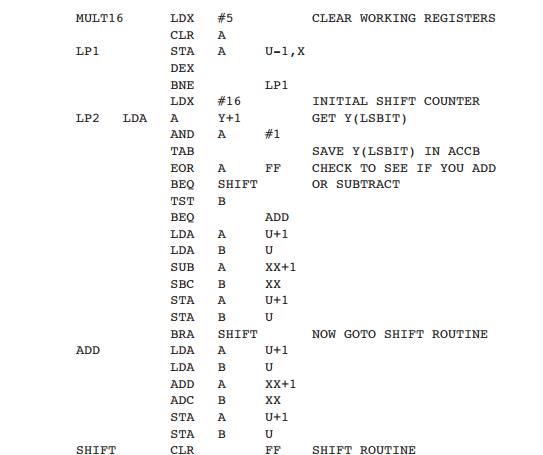
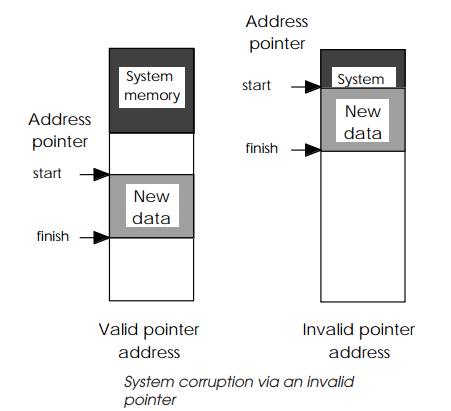
The code example is a routine for performing a simple 16 bit
multiplication. It takes two unsigned 16 bit numbers and produces a 16 bit
product. If the product is larger than 16 bits, only the least significant 16
bits are retained. The first eight or so instructions simply create a temporary
storage area on the stack for the multiplicand, multiplier, return address and
loop counter. Com-pared to internal register storage, storing data in stack
frames is not as efficient due the increased external memory access.
Accessing external data consumes machine cycles which could be used to
process data. Without suitable registers and the 16 bit wide accumulator, all
this information must be stored externally on the stack. The algorithm used
simply performs a succession of arithmetic shifts on each half of the
multiplicand stored in the A and B accumulators. Once this is complete, the 16
bit result is split between the two accumulators and the temporary storage
cleared off the stack. The operation takes at least 29 instructions to perform
with the actual execution time totally dependant on the values being multiplied
together. For compari-son, most 16/32 bit processors such as the MC68000 and
80x86 families can perform the same operation with a single instruction!
Addressing memory
When the first 8 bit microprocessors appeared during the middle to late
1970s, memory was expensive and only available in very small sizes: 256 bytes
up to 1 kilobyte. Applications were small, partly due to their implementation
in assembler rather than a high level language, and therefore the addressing
range of 64 kilobytes offered by the 16 bit address seemed extraordinarily
large. It was unlikely to be exceeded. As the use of these early
microprocessors became more widespread, applications started to grow in size
and the use of operating systems like CP/M and high level languages increased
memory requirements until the address range started to limit applications.
Various techniques like bank switching and program overlays were developed to
help.
System integrity
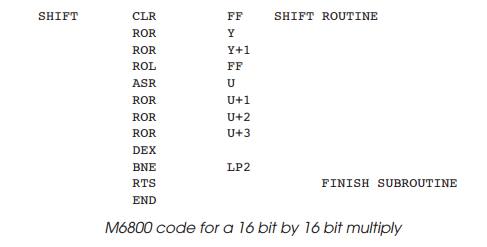
Another disadvantage with this type of architecture is its
unpredictability in handling error conditions. A bug in a software application
could corrupt the whole system, causing a system to either crash, hang up or,
even worse, perform some unforeseen operations. The reasons are quite simple:
there is no partitioning between data and programs within the architecture. An
applica-tion can update a data structure using a corrupt index pointer which
overwrites a part of its program.
Data are simply bytes of information which can be inter-preted as
instruction codes. The processor calls a subroutine within this area, starts to
execute the data as code and suddenly the whole system starts performing
erratically! On some machines, certain undocumented code sequences could put
the processor in a test mode and start cycling through the address ranges etc.
These attributes restricted their use to non-critical applications.
Related Topics