Chapter: Security in Computing : Security in Networks
Example Firewall Configurations
Example Firewall Configurations
Let us look at several
examples to understand how to use firewalls. We present situations designed to
show how a firewall complements a sensible security policy and architecture.
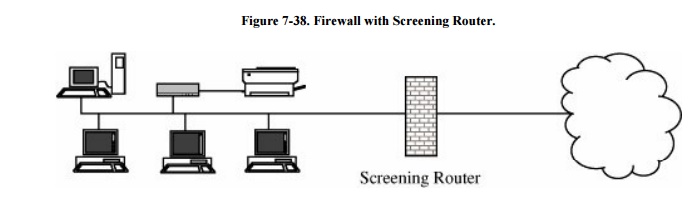
The simplest use of a
firewall is shown in Figure 7-38. This
environment has a screening router positioned between the internal LAN and the
outside network connection. In many cases, this installation is adequate when
we need only screen the address of a router.
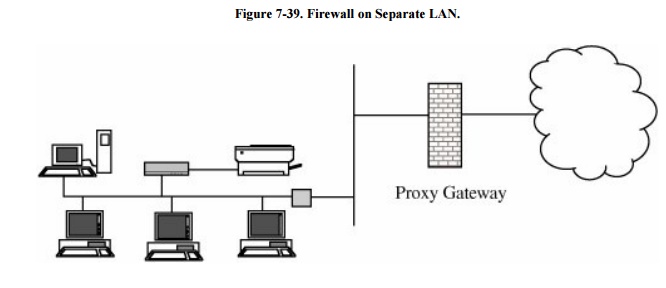
However, to use a proxy
machine, this organization is not ideal. Similarly, configuring a router for a
complex set of approved or rejected addresses is difficult. If the firewall
router is successfully attacked, then all traffic on the LAN to which the
firewall is connected is visible. To reduce this exposure, a proxy firewall is
often installed on its own LAN, as shown in Figure
7-39. In this way the only traffic visible on that LAN is the
traffic going into and out of the firewall.
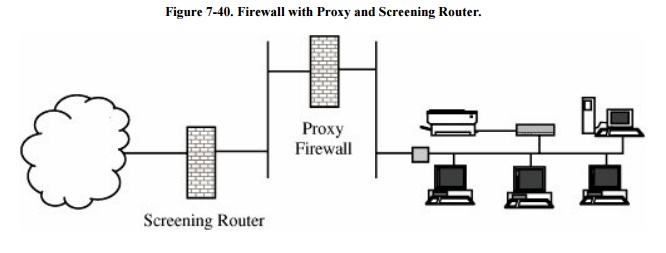
For even more protection, we
can add a screening router to this configuration, as shown in Figure 7-40. Here, the screening router ensures
address correctness to the proxy firewall (so that the proxy firewall cannot be
fooled by an outside attacker forging an address from an inside host); the
proxy firewall filters traffic according to its proxy rules. Also, if the
screening router is subverted, only the traffic to the proxy firewall is
visiblenot any of the sensitive information on the internal protected LAN.
Although these examples are
simplifications, they show the kinds of configurations firewalls protect. Next,
we review the kinds of attacks against which firewalls can and cannot protect.
What Firewalls Canand CannotBlock
As we have seen, firewalls
are not complete solutions to all computer security problems. A firewall
protects only the perimeter of its environment against attacks from outsiders
who want to execute code or access data on the machines in the protected
environment. Keep in mind these points about firewalls.
Firewalls can protect an
environment only if the firewalls control the entire perimeter. That is,
firewalls are effective only if no unmediated connections breach the perimeter.
If even one inside host connects to an outside address, by a modem for example,
the entire inside net is vulnerable through the modem and its host.
Firewalls do not protect data
outside the perimeter; data that have properly passed (outbound) through the
firewall are just as exposed as if there were no firewall.
Firewalls are the most
visible part of an installation to the outside, so they are the most attractive
target for attack. For this reason, several different layers of protection,
called defense in depth, are better
than relying on the strength of just a single firewall.
Firewalls must be correctly
configured, that configuration must be updated as the internal and external
environment changes, and firewall activity reports must be reviewed
periodically for evidence of attempted or successful intrusion.
Firewalls are targets for
penetrators. While a firewall is designed to withstand attack, it is not
impenetrable. Designers intentionally keep a firewall small and simple so that
even if a penetrator breaks it, the firewall does not have further tools, such
as compilers, linkers, loaders, and the like, to continue an attack.
Firewalls exercise only minor
control over the content admitted to the inside, meaning that inaccurate data
or malicious code must be controlled by other means inside the perimeter.
Firewalls are important tools
in protecting an environment connected to a network. However, the environment
must be viewed as a whole, all possible exposures must be considered, and the
firewall must fit into a larger, comprehensive security strategy. Firewalls
alone cannot secure an environment.
Related Topics