Chapter: Cryptography and Network Security
Simple Hash Functions
SIMPLE HASH FUNCTIONS
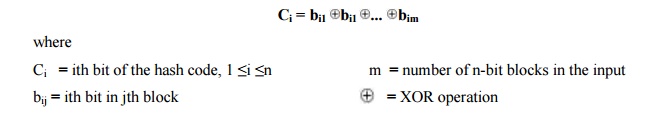
All hash functions operate using the following general principles. The input (message, file, etc.) is viewed as a sequence of n-bit blocks. The input is processed one block at a time in an iterative fashion to produce an n-bit hash function.
One of
the simplest hash functions is the bit-by-bit exclusive-OR (XOR) of every
block. This can be expressed as follows:
Thus, the
probability that a data error will result in an unchanged hash value is 2n.
With more predictably formatted data, the function is less effective. For
example, in most normal text files, the high-order bit of each octet is always
zero. So if a 128-bit hash value is used, instead of an effectiveness of 2128,
the hash function on this type of data has an effectiveness of 2112.
A simple way to improve matters is to
perform a one-bit circular shift, or rotation, on the hash value after each block is processed. The procedure can be
summarized as follows:
Initially
set the n-bit hash value to zero.
Process
each successive n-bit block of data as follows:
i.
Rotate the current hash value to the left by one
bit.
ii.
XOR the block into the hash value.
Related Topics