Chapter: Cryptography and Network Security
Classical CryptoSystems
CLASSICAL CRYPTO SYSTEMS
1 CONVENTIONAL ENCRYPTION
referred conventional / private-key / single-key
sender
and recipient share a common key
all
classical encryption algorithms are private-key
was only
type prior to invention of public-key in 1970‟plaintext - the
original message
Some basic terminologies used :
ciphertext - the coded message
cipher - algorithm for transforming plaintext
to ciphertext
key - info used in cipher known only
to sender/receiver
encipher (encrypt) -
converting plaintext to ciphertext
decipher (decrypt) -
recovering ciphertext from plaintext
cryptography - study of encryption
principles/methods
cryptanalysis (codebreaking) - the
study of principles/ methods of deciphering ciphertext without knowing key
cryptology - the field of both cryptography
and cryptanalysis
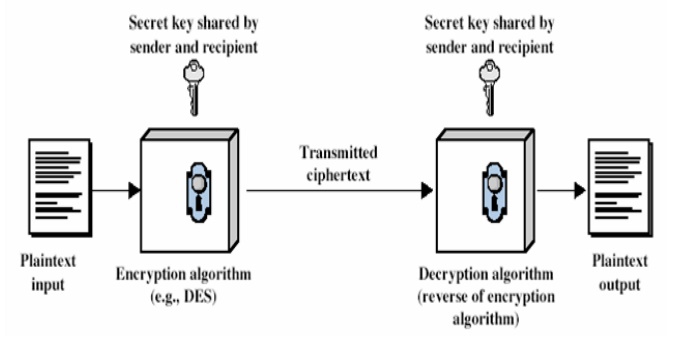
Figure 1.3.1.1: Conventional
Encryption
Here the
original message, referred to as plaintext, is converted into apparently random
nonsense, referred to as cipher text. The encryption process consists of an
algorithm and a key. The key is a value independent of the plaintext. Changing
the key changes the output of the algorithm. Once the cipher text is produced,
it may be transmitted. Upon reception, the cipher text can be transformed back
to the original plaintext by using a decryption algorithm and the same key that
was used for encryption.
The
security depends on several factors. First, the encryption algorithm must be
powerful enough that it is impractical to decrypt a message on the basis of
cipher text alone. Beyond that, the security depends on the secrecy of the key,
not the secrecy of the algorithm.
Two requirements for secure use of symmetric
encryption:
a strong
encryption algorithm
a secret
key known only to sender / receiver
Y = EK(X)
= DK(Y)
assume encryption algorithm is known
implies a secure channel to distribute key
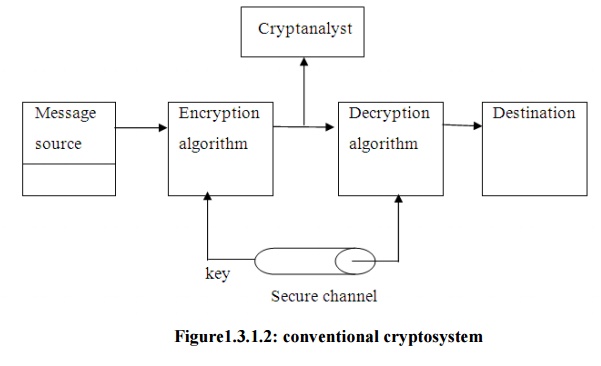
A source
produces a message in plaintext, X = [X1, X2, … , XM] where M are the number of
letters in the message. A key of the form K = [K1, K2, …, KJ] is generated. If
the key is generated at the source, then it must be provided to the destination
by means of some secure channel.
With the
message X and the encryption key K as input, the encryption algorithm forms the
cipher text Y = [Y1, Y2, …, YN]. This can be expressed as
Y = EK(X)
The
intended receiver, in possession of the key, is able to invert the
transformation: X = DK(Y)
An
opponent, observing Y but not having access to K or X, may attempt to recover X
or K or both. It is assumed that the opponent knows the encryption and
decryption algorithms. If the opponent is interested in only this particular
message, then the focus of effort is to recover X by generating a plaintext
estimate. Often if the opponent is interested in being able to read future
messages as well, in which case an attempt is made to recover K by generating
an estimate.
Cryptography
Cryptographic
systems are generally classified along 3 independent dimensions:
Type of operations used for transforming plain text
to cipher text
All the
encryption algorithms are abased on two general principles: substitution, in which each element in
the plaintext is mapped into another element, and transposition, in which elements in the plaintext are rearranged.
The number of keys used
If the
sender and receiver uses same key then it is said to be symmetric key (or) single key
(or) conventional encryption.
If the
sender and receiver use different keys then it is said to be public key encryption.
The way in which the plain text is processed
A block cipher processes the input and
block of elements at a time, producing output block for each input block.
A stream cipher processes the input
elements continuously, producing output element one at a time, as it goes
along.
Cryptanalysis
The
process of attempting to discover X or K or both is known as cryptanalysis. The
strategy used by the cryptanalysis depends on the nature of the encryption
scheme and the information available to the cryptanalyst.
There are various types of cryptanalytic attacks based on the amount of
information
known to the cryptanalyst.
Cipher text only – A copy of cipher text alone is known to the cryptanalyst.
Known plaintext – The cryptanalyst has a copy of the cipher text and the
corresponding plaintext.
Chosen plaintext – The cryptanalysts gains temporary access to the encryption
machine. They cannot open it to find
the key, however; they can encrypt a large number of suitably chosen plaintexts
and try to use the resulting cipher texts to deduce the key.
Chosen cipher text – The cryptanalyst obtains temporary
access to the decryption machine,
uses it to decrypt several string of symbols, and tries to use the results to
deduce the key.
2 STEGANOGRAPHY
A
plaintext message may be hidden in any one of the two ways. The methods of
steganography conceal the existence of the message, whereas the methods of
cryptography render the message unintelligible to outsiders by various
transformations of the text.
A simple
form of steganography, but one that is time consuming to construct is one in
which an arrangement of words or letters within an apparently innocuous text
spells out the real message.
Example:
the
sequence of first letters of each word of the overall message spells out the
real (hidden) message.
Subset of
the words of the overall message is used to convey the hidden message. Various
other techniques have been used historically, some of them are:
Character marking – selected letters of printed or
typewritten text are overwritten in pencil.
The marks are ordinarily not visible unless the paper is held to an angle to
bright light.
Invisible ink – a number of substances can be used for writing but leave no
visible trace until heat or some
chemical is applied to the paper.
Pin punctures – small pin punctures on selected letters are ordinarily not visible
unless the paper is held in front of
the light.
Typewritten correction ribbon – used between the lines typed with a
black ribbon, the results of typing
with the correction tape are visible only under a strong light.
Drawbacks of steganography
Requires a lot of overhead to hide a relatively few bits of information.
Once the system is discovered, it becomes virtually worthless.
Related Topics