Chapter: Computer Networks : Application Layer
Important Questions and Answers : Networks - Application Layer
1. What is the function of SMTP?
The TCP/IP protocol supports electronic mail on the Internet is called Simple Mail Transfer (SMTP). It is a system for sending messages to other computer users based
on e-mail addresses. SMTP provides mail exchange between users on the same or different computers.
2. What is the difference between a user agent (UA) and a mail transfer agent (MTA)?
The UA prepares the message, creates the envelope, and puts the message in the envelope. The MTA transfers the mail across the Internet.
3. How does MIME enhance SMTP?
MIME is a supplementary protocol that allows non-ASCII data to be sent through SMTP. MIME transforms non-ASCII data at the sender site to NVT ASCII data and deliverers it to the client SMTP to be sent through the Internet. The server SMTP at the receiving side receives the NVT ASCII data and delivers it to MIME to be transformed back to the original data.
4. Why is an application such as POP needed for electronic messaging?
Workstations interact with the SMTP host, which receives the mail on behalf of every host in the organization, to retrieve messages by using a client-server protocol such as Post Office Protocol, version 3(POP3). Although POP3 is used to download messages from the server, the SMTP client still needed on the desktop to forward messages from the workstation user to its SMTP mail server.
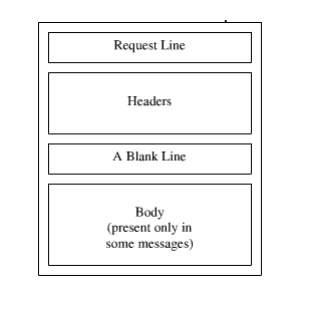
5. Give the format of HTTP request message?
6. What is the purpose of Domain Name System?
Domain Name System can map a name to an address and conversely an address to name.
7. Discuss the three main division of the domain name space.
Domain name space is divided into three different sections: generic domains, country domains & inverse domain.
Generic domain: Define registered hosts according to their generic behavior, uses generic suffixes.
Country domain: Uses two characters to identify a country as the last suffix.
Inverse domain: Finds the domain name given the IP address.
8. Discuss the TCP connections needed in FTP.
FTP establishes two connections between the hosts. One connection is used for data transfer, the other for control information. The control connection uses very simple rules of communication. The data connection needs more complex rules due to the variety of data types transferred.
9. Discuss the basic model of FTP.
The client has three components: the user interface, the client control process, and the client data transfer process. The server has two components: the server control process and the server data transfer process. The control connection is made between the control processes. The data connection is made between the data transfer processes.
10. Name four factors needed for a secure network?
Privacy: The sender and the receiver expect confidentiality.
Authentication: The receiver is sure of the sender’s identity and that an imposter has not sent the message.
Integrity: The data must arrive at the receiver exactly as it was sent.
Non-Reputation: The receiver must able to prove that a received message came from a specific sender.
11. How is a secret key different from public key?
In secret key, the same key is used by both parties. The sender uses this key and an encryption algorithm to encrypt data; the receiver uses the same key and the corresponding decryption algorithm to decrypt the data. In public key, there are two keys: a private key and a public key. The private key is kept by the receiver. The public key is announced to the public.
12. What is a digital signature?
Digital signature is a method to authenticate the sender of a message. It is similar to that of signing transactions documents when you do business with a bank. In network transactions, you can create an equivalent of an electronic or digital signature by the way you send data.
13. What are the advantages & disadvantages of public key encryption?
Advantages:
a) Remove the restriction of a shared secret key between two entities. Here each entity can create a pair of keys, keep the private one, and publicly distribute the other one.
b) The no. of keys needed is reduced tremendously. For one million users to communicate, only two million keys are needed.
Disadvantage:
If you use large numbers the method to be effective. Calculating the cipher text using the long keys takes a lot of time. So it is not recommended for large amounts of text.
14. What are the advantages & disadvantages of secret key encryption?
Advantage:
Secret Key algorithms are efficient: it takes less time to encrypt a message. The reason is that the key is usually smaller. So it is used to encrypt or decrypt long messages.
Disadvantages:
a) Each pair of users must have a secret key. If N people in world want to use this method, there needs to be N (N-1)/2 secret keys. For one million people to communicate, a half-billion secret keys are needed.
b) The distribution of the keys between two parties can be difficult.
15. Define permutation.
Permutation is transposition in bit level.
Straight permutation: The no. of bits in the input and output are preserved.
Compressed permutation: The no. of bits is reduced (some of the bits are dropped).
Expanded permutation: The no. of bits is increased (some bits are repeated).
16. Define substitution & transposition encryption?
. Substitution: A character level encryption in which each character is replaced by another character in the set.
Transposition: A Character level encryption in which the characters retain their plaintext but the position of the character changes.
17. Define CGI?
. CGI is a standard for communication between HTTP servers and executable programs. It is used in crating dynamic documents.
18. What are the requests messages support SNMP and explain it?
· GET
· SET
The former is used to retrieve a piece of state from some node and the latter is used to store a new piece of state in some node.
19. Define PGP?
Pretty Good Privacy is used to provide security for electronic mail. It provides authentication, confidentiality, data integrity, and non repudiation.
20. Define SSH?
Secure Shell is used to provide a remote login, and used to remotely execute commands and transfer files and also provide strong client/server authentication / message integrity.
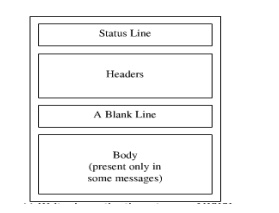
21. Give the format of HTTP response message?
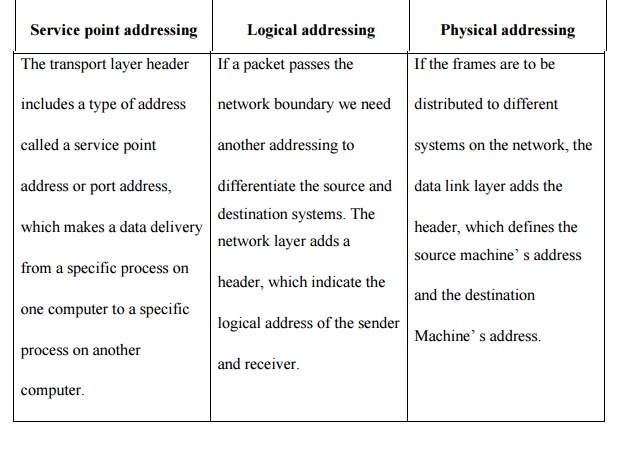
22. What is the difference between service point address, logical address and physical address? Service point addressing Logical addressing Physical addressing
21. Discuss the basic model of FTP.
The client has three components: the user interface, the client control process, and the client data transfer process. The server has two components: the server control process and the server data transfer process. The control connection is made between the control processes. The data connection is made between the data transfer processes.
22.What is a digital signature?
Digital signature is a method to authenticate the sender of a message. It is similar to that of signing transactions documents when you do business with a bank. In network transactions, you can create an equivalent of an electronic or digital signature by the way you send data.
23.Draw the diagram foe explain security
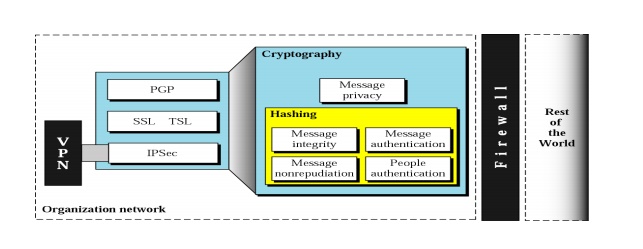
24. Define Cryptography
n Cryptography refers to the science and art of transforming messages to make them secure and immune to attacks.
n Original message before being transformed is called plaintext.
n After the message is transformed, is called ciphertext.
n An encryption algorithm transforms the plaintext to ciphertext; a decryption algorithm transforms the ciphertext back to plaintext.
n The term cipher is used to refer to encryption and decryption algorithms.
25. What are the types of DNS Message
n Two types of messages
Query: header and question records
n Response: Header, question records, answer records, authoritative records, and additional records.
26. What is TELNET PROTOCOL?
A TELNET connection is a Transmission Control Protocol (TCP) connection used to transmit data with interspersed TELNET control information.
The TELNET Protocol is built upon three main ideas: first, the concept of a "Network
Virtual Terminal"; second, the principle of negotiated options; and third, a symmetric view of terminals and processes.
27. What is PGP?
Pretty Good Privacy. A program using public key encryption popularly used with email
A high security RSA public-key encryption application for MS-DOS, Unix, VAX/VMS, and other computers. It was written by Philip R. Zimmermann of Phil's Pretty Good(tm) Software and later augmented by a cast of thousands, especially including Hal Finney, Branko Lankester, and Peter Guttmann.
28. What is POP3?
POP3 (Post Office Protocol 3) is the most recent version of a standard protocol for receiving e-mail. POP3 is a client/server protocol in which e-mail is received and held for you by your Internet server. POP and IMAP deal with the receiving of e-mail and are not to be confused with the Simple Mail Transfer Protocol (SMTP), a protocol for transferring e-mail across the Internet.
29. What is IMAP.
IMAP (Internet Message Access Protocol) is a standard protocol for accessing e-mail from your local server. IMAP (the latest version is IMAP Version 4) is a client/server protocol in which e-mail is received and held for you by your Internet server.
IMAP can be thought of as a remote file server. POP3 can be thought of as a "store-and-forward" service.
30. What is SSH?
(Secure Shell) A security protocol for logging into a remote server. SSH provides an encrypted session for transferring files and executing server programs. Also serving as a secure client/server connection for applications such as database access and e-mail SSH supports a variety of authentication methods.
Related Topics