Chapter: Multicore Application Programming For Windows, Linux, and Oracle Solaris : Identifying Opportunities for Parallelism
Hosting Multiple Operating Systems Using Hypervisors
Hosting
Multiple Operating Systems Using Hypervisors
Two other approaches that enforce better isolation between guests’
operating systems also remove the restriction that the guests run the same
operating system as the host. These approaches are known as type 1 and type 2 hypervisors.
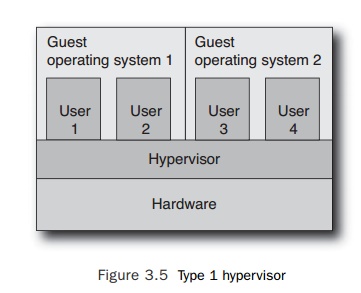
Type 1 hypervisors replace the host operating system with a very
lightweight but high-level system supervisor system, or hypervisor, that can load and initiate multiple operating system
instances on its own. Each operating system instance is entirely isolated from
the others while sharing the same hardware.
Each operating system appears to have access to its own machine. It is
not apparent, from within the operating system, that the hardware is being
shared. The hardware has effectively been virtualized,
in that the guest operating system will believe it is running on whatever type
of hardware the hypervisor indicates.
This provides the isolation that is needed for ensuring both security
and robustness, while at the same time making it possible to run multiple
copies of different operating systems as guests on the same host. Each guest
believes that the entire hardware resources of the machine are available.
Examples of this kind of hypervisor are the Logical Domains provided on the Sun
UltraSPARC T1 and T2 product lines or the Xen hyper-visor software on x86.
Figure 3.5 illustrates a type 1 hypervisor.
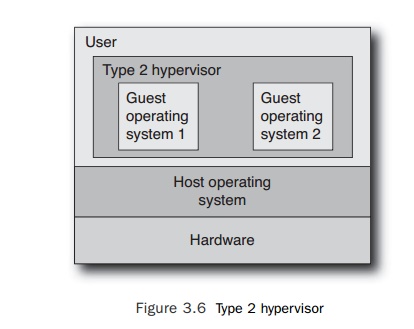
A type 2 hypervisor is actually a normal user application running on top
of a host operating system. The hypervisor software is architected to host
other operating systems. Good examples of type 2 hypervisors are the open
source VirtualBox software, VMware, or the Parallels software for the Apple
Macintosh. Figure 3.6 illustrates a type 2 hypervisor.
Clearly, it is also possible to combine these strategies and have a
system that supports multiple levels of virtualization, although this might not
be good for overall performance.
Even though these strategies are complex, it is worth exploring why
virtualization is an appealing technology.
n
Security. In a virtualized or containerized
environment, it is very hard for an application
in one virtualized operating system to obtain access to data held in a
different one. This also applies to operating systems being hacked; the
damage that a hacker can do is constrained by what is visible to them from the
operating sys-tem that they hacked into.
Robustness. With virtualization, a fault in a guest operating system can affect only those applications running on
that operating system, not other applications running in other guest operating
systems.
n
Configuration isolation. Some
applications expect to be configured in particular ways: They might always expect to be installed in the same place
or find their con-figuration parameters in the same place. With virtualization,
each instance believes it has the entire system to itself, so it can be
installed in one place and not interfere with another instance running on the
same host system in a different virtualized container.
n Restricted control. A user or application can be given root access to an instance of a virtualized operating system, but
this does not give them absolute control over the entire system.
n Replication. There are situations, such as running a computer lab, where it is
nec-essary to be able to quickly reproduce multiple instances of an identical
configura-tion. Virtualization can save the effort of performing clean
reinstalls of an operating system. A new guest operating system can be started,
providing a new instance of the operating system. This new instance can even
use a preconfigured image, so it can be up and running easily.
n Experimentation. It is very easy to distribute a virtualized image of an operating system. This means a user can try a
new operating system without doing any dam-age to their existing configuration.
n Hardware isolation. In some cases, it is possible to take the running image of a virtualized operating system and move
that to a new machine. This means that old or broken hardware can be switched
out without having to make changes to the software running on it.
Scaling. It is possible to dynamically respond to increased requests for work
by starting up more virtual images.
For example, a company might provide a web-hosted computation on-demand
service. Demand for the service might peak on weekday evenings but be very low
the rest of the time. Using virtualization, it would be
possible to start up new virtual machines to handle the load at the times when
the demand increases.
n Consolidation. One of the biggest plays for virtualization is that of consolidating multiple old machines down to fewer new machines. Virtualization can take the existing applications, and their host operating systems can move them to a new host. Since the application is moved with its host operating system, the transition is more likely to be smooth than if the application had to be reconfigured for a new environment.
All these characteristics of virtualization make it a good fit for cloud computing. Cloud computing is a
service provided by a remote farm of machines. Using virtualization, each user
can be presented with root access to an unshared virtual machine. The number of
machines can be scaled to match the demand for their service, and new machines
can quickly be brought into service by replicating an existing setup. Finally,
the software is isolated from the physical hardware that it is running on, so
it can easily be moved to new hardware as the farm evolves.
Related Topics