Chapter: Security in Computing : Administering Security
Risk Analysis
Risk Analysis
Good, effective security
planning includes a careful risk analysis. A risk is a potential problem that
the system or its users may experience. We distinguish a risk from other
project events by looking for three things, as suggested by Rook [ROO93]:
A loss associated with an event. The event must generate a negative
effect: compromised security, lost time, diminished quality, lost money, lost
control, lost understanding, and so on. This loss is called the risk impact.
The likelihood that the event will occur. The probability of
occurrence associated with each risk is measured from 0 (impossible) to 1
(certain). When the risk probability is 1, we say we have a problem.
The degree to which we can change the outcome. We must determine
what, if anything, we can do to avoid the impact or at least reduce its
effects. Risk control involves a set of actions to reduce or eliminate the
risk. Many of the security controls we describe in this book are examples of
risk control.
We usually want to weigh the
pros and cons of different actions we can take to address each risk. To that
end, we can quantify the effects of a risk by multiplying the risk impact by
the risk probability, yielding the risk exposure. For example, if the
likelihood of virus attack is 0.3 and the cost to clean up the affected files
is $10,000, then the risk exposure is $3,000. So we can use a calculation like
this one to decide that a virus checker is worth an investment of $100, since
it will prevent a much larger potential loss. Clearly, risk probabilities can
change over time, so it is important to track them and plan for events
accordingly.
Risk is inevitable in life:
Crossing the street is risky but that does not keep us from doing it. We can
identify, limit, avoid, or transfer risk but we can seldom eliminate it. In
general, we have three strategies for dealing with risk:
avoiding the risk, by changing
requirements for security or other system characteristics
transferring the risk, by allocating the
risk to other systems, people, organizations, or assets; or by buying insurance
to cover any financial loss should
the risk become a reality
assuming the risk, by accepting it,
controlling it with available resources, and preparing to deal with the loss if
it occurs
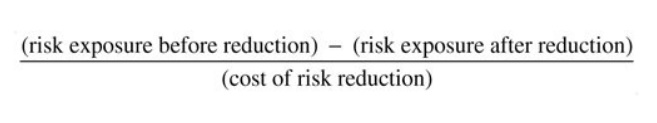
Thus, costs are associated
not only with the risk's potential impact but also with reducing it. Risk leverage is the difference in risk
exposure divided by the cost of reducing the risk. In other words, risk
leverage is
If the leverage value of a proposed
action is not high enough, then we look for alternative but less costly actions
or more effective reduction techniques.
Risk analysis is the process
of examining a system and its operational context to determine possible
exposures and the potential harm they can cause. Thus, the first step in a risk
analysis is to identify and list all exposures in the computing system of
interest. Then, for each exposure, we identify possible controls and their
costs. The last step is a costbenefit analysis: Does it cost less to implement
a control or to accept the expected cost of the loss? In the remainder of this
section, we describe risk analysis, present examples of risk analysis methods,
and discuss some of the drawbacks to performing risk analysis.
Related Topics