Chapter: Security in Computing : Administering Security
Contents of a Security Plan
Contents of a Security Plan
A security plan identifies
and organizes the security activities for a computing system. The plan is both
a description of the current situation and a plan for improvement. Every
security plan must address seven issues.
policy, indicating the goals of a
computer security effort and the willingness of the people involved to work to achieve
those goals
current state, describing the status of security at the time of the
plan
requirements, recommending ways to meet the security goals
recommended controls, mapping controls to the vulnerabilities
identified in the policy and requirements
accountability, describing who is responsible for each security
activity
timetable, identifying when different security functions are to be
done
continuing attention, specifying a structure for periodically
updating the security plan
There are many approaches to
creating and updating a security plan. Some organizations have a formal,
defined security planning process, much as they might have a defined and
accepted development or maintenance process. Others look to security
professionals for guidance on how to perform security planning. For example, Sidebar 8 -1 describes a security planning
methodology suggested by the U.S. Software Engineering Institute and made
available on its web site. But every security plan contains the same basic
material, no matter the format. The following sections expand on the seven
parts of a security plan.
1. Policy
A security plan must state
the organization's policy on security. A security policy is a high-level
statement of purpose and intent. Initially, you might think that all policies
would be the same: to prevent security breaches. But in fact the policy is one
of the most difficult sections to write well. As we discuss later in this
chapter, there are tradeoffs among the strength of the security, the cost, the
inconvenience to users, and more.
Sidebar 8-1: The OCTAVESM Methodology
The Software Engineering Institute at
Carnegie Mellon University has created a framework for building a security
plan. (See [ALB99, ALB01].) The framework, called OCTAVE,
includes eight steps:
·
Identify enterprise knowledge.
·
Identify operational area
knowledge.
·
Identify staff knowledge.
·
Establish security
requirements.
·
Map high-priority information
assets to information infrastructure.
·
Perform an infrastructure vulnerability
evaluation.
·
Conduct a multidimensional
risk analysis.
·
Develop a protection strategy.
These steps lead a project manager or security analyst in determining
the security risks and finding controls to address them. The OCTAVE web site (www.cert.org/octave)
contains detailed information and checklists to guide the planning process.
For example, we must decide
whether to implement very stringentand possibly unpopularcontrols that prevent
all security problems or simply mitigate the effects of security breaches once
they happen. For this reason, the policy statement must answer three essential
questions:
oWho should be allowed access?
oTo what system and organizational resources should access be
allowed?
oWhat types of access should each user be allowed for each resource?
The policy statement should
specify the following:
The organization's goals on
security. For example, should the system protect data from leakage to
outsiders, protect against loss of data due to physical disaster, protect the
data's integrity, or protect against loss of business when computing resources
fail? What is the higher priority: serving customers or securing data?
Where the responsibility for
security lies. For example, should the responsibility rest with a small
computer security group, with each employee, or with relevant managers?
The organization's commitment
to security. For example, who provides security support for staff, and where
does security fit into the organization's structure?
Current Security Status
To be able to plan for
security, an organization must understand the vulnerabilities to which it may
be exposed. The organization can determine the vulnerabilities by performing a
risk analysis: a careful investigation of the system, its environment, and the
things that might go wrong. The risk analysis forms the basis for describing
the current status of security. The status can be expressed as a listing of
organizational assets, the security threats to the assets, and the controls in
place to protect the assets. We look at risk analysis in more detail later in
this chapter.
The status portion of the
plan also defines the limits of responsibility for security. It describes not
only which assets are to be protected but also who is responsible for
protecting them. The plan may note that some groups may be excluded from
responsibility; for example, joint ventures with other organizations may
designate one organization to provide security for all member organizations.
The plan also defines the boundaries of responsibility, especially when
networks are involved. For instance, the plan should clarify who provides the
security for a network router or for a leased line to a remote site.
Even though the security plan
should be thorough, there will necessarily be vulnerabilities that are not
considered. These vulnerabilities are not always the result of ignorance or
naïveté; rather, they can arise from the addition of new equipment or data as
the system evolves. They can also result from new situations, such as when a
system is used in ways not anticipated by its designers. The security plan
should detail the process to be followed when someone identifies a new
vulnerability. In particular, instructions should explain how to integrate
controls for that vulnerability into the existing security procedures.
3. Requirements
The heart of the security
plan is its set of security requirements:
functional or performance demands placed on a system to ensure a desired level
of security. The requirements are usually derived from organizational needs.
Sometimes these needs include the need to conform to specific security
requirements imposed from outside, such as by a government agency or a
commercial standard.
Pfleeger [PFL91] points out that we must distinguish the
requirements from constraints and controls. A constraint is an aspect of the security policy that constrains,
circumscribes, or directs the implementation of the requirements. As we learned
in Chapter 1, a control is an action, device, procedure, or technique that removes
or reduces a vulnerability. To see the difference between requirements,
constraints, and controls, consider the six "requirements" of the
U.S. Department of Defense's TCSEC, introduced in Chapter
5. These six items are listed in Table
8-1.
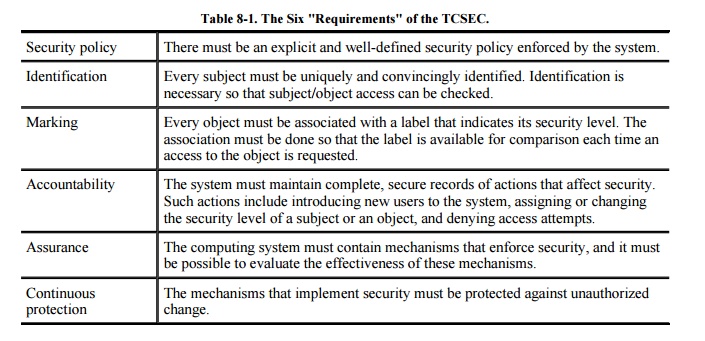
Given our definitions of
requirement, constraint, and control, it is easy to see that the first
"requirement" of the TCSEC is really a constraint: the security
policy. The second and third "requirements" describe mechanisms for
enforcing security, not descriptions of required behaviors. That is, the second
and third "requirements" describe explicit implementations, not a
general characteristic or property that the system must have. However, the
fourth, fifth, and sixth TCSEC "requirements" are indeed true
requirements. They state that the system must have certain characteristics, but
they do not enforce a particular implementation.
These distinctions are
important because the requirements explain what should be accomplished, not
how. That is, the requirements should always leave the implementation details
to the designers, whenever possible. For example, rather than writing a
requirement that certain data records should require passwords for access (an
implementation decision), a security planner should state only that access to
the data records should be restricted (and note to whom the access should be
restricted). This more flexible requirement allows the designers to decide
among several other access controls (such as access control lists) and to
balance the security requirements with other system requirements, such as
performance and reliability. Figure 8-1
illustrates how the different aspects of system analysis support the security
planning process.

As with the general software
development process, the security planning process must allow customers or
users to specify desired functions, independent of the implementation. The
requirements should address all aspects of security: confidentiality,
integrity, and availability. They should also be reviewed to make sure that
they are of appropriate quality. In particular, we should make sure that the
requirements have these characteristics:
Correctness: Are the requirements understandable? Are they stated without error?
Consistency: Are there any conflicting or ambiguous requirements?
Completeness: Are all
possible situations addressed by the requirements?
Realism: Is it possible to implement what the requirements mandate?
Need: Are the requirements unnecessarily restrictive?
Verifiability: Can tests be written to demonstrate conclusively and objectively
that the requirements have been met? Can the
system or its functionality be measured in some way that will assess the
degree to which the requirements are met?
Traceability: Can each requirement be traced to the functions and data related to
it so that changes in a requirement can lead to easy reevaluation?
The requirements may then be
constrained by budget, schedule, performance, policies, governmental
regulations, and more. Given the requirements and constraints, the developers
then choose appropriate controls.
4. Recommended Controls
The security requirements lay
out the system's needs in terms of what should be protected. The security plan
must also recommend what controls should be incorporated into the system to
meet those requirements. Throughout this book you have seen many examples of
controls, so we need not review them here. As we see later in this chapter, we
can use risk analysis to create a map from vulnerabilities to controls. The
mapping tells us how the system will meet the security requirements. That is,
the recommended controls address implementation issues: how the system will be
designed and developed to meet stated security requirements.
5. Responsibility for Implementation
A section of the security
plan should identify which people are responsible for implementing the security
requirements. This documentation assists those who must coordinate their
individual responsibilities with those of other developers. At the same time,
the plan makes explicit who is accountable should some requirement not be met
or some vulnerability not be addressed. That is, the plan notes who is
responsible for implementing controls when a new vulnerability is discovered or
a new kind of asset is introduced. (But see Sidebar
8-2 on who is responsible.)
People building, using, and
maintaining the system play many roles. Each role can take some responsibility
for one or more aspects of security. Consider, for example, the groups listed
here.
Personal computer users may
be responsible for the security of their own machines. Alternatively, the
security plan may designate one person or group to be coordinator of personal
computer security.
Project leaders may be
responsible for the security of data and computations.
Sidebar
8-2: Who Is Responsible for Using Security?
We put a lot of responsibility on the
user: Apply these patches, don't download unknown code, keep sensitive material
private, change your password frequently, don't forget your umbrella. We are
all fairly technology-savvy, so we take in stride messages like "fatal
error." (A neighbor once called in a panic that her entire machine and all
its software data were about to go up in a puff of electronic smoke because she
had received a "fatal error" message; I explained calmly that the
message was perhaps a bit melodramatic.)
But that neighbor raises an important
point: how can we expect users to use their computers securely when that is so
hard to do? Take, for example, the various steps necessary in securing a
wireless access point (see Chapter 7): Use WPA or WPA2, not WEP; set the
access point into nonbroadcast mode, not open; choose a random 128-bit number
for an initial value. Whitten and Tygar [WHI99] list four points
critical to users' security: users must be
aware of the security of tasks they need to perform
able to figure out how to perform those tasks successfully
prevented from making dangerous errors
sufficiently comfortable with the technology to continue using it
Whitten and Tygar conclude that the
popular PGP product, which has a fairly good user interface, is not usable
enough to provide effective security for most computer users. Furnell [FUR05]
reached a similar conclusion about the security features in Microsoft Word.
The field of humancomputer interaction
(HCI) is mature, guidance materials are available, and numerous good examples
exist. Why, then, are security settings hidden on a sub-sub-tab and written in
highly technical jargon? We cannot expect users to participate in security
enforcement unless they can understand what they should do.
A leader in the HCI field, Ben
Shneiderman counsels that the humancomputer interface should be, in his word,
fun. Citing work others have done on computer game interfaces, Shneiderman
notes that such interfaces satisfy needs for challenge, curiosity, and fantasy.
He then argues that computer use must "(1) provide the right functions so
that users can accomplish their goals, (2) offer usability plus reliability to
prevent frustration from undermining the fun, and (3) engage users with
fun-features." [SHN04]
One can counter that security
functionality is serious, unlike computer games or web browsers. Still, this
does not relieve us from the need to make the interface consistent,
informative, empowering, and errorpreventing.
Managers may be responsible
for seeing that the people they supervise implement security measures.
Database administrators may
be responsible for the access to and integrity of data in their databases.
Information officers may be
responsible for overseeing the creation and use of data; these officers may
also be responsible for retention and proper disposal of data.
Personnel staff members may
be responsible for security involving employees, for example, screening
potential employees for trustworthiness and arranging security training
programs.
Timetable
A comprehensive security plan
cannot be executed instantly. The security plan includes a timetable that shows
how and when the elements of the plan will be performed. These dates also give
milestones so that management can track the progress of implementation.
If the implementation is to
be a phased development (that is, the system will be implemented partially at
first, and then changed functionality or performance will be added in later
releases), the plan should also describe how the security requirements will be
implemented over time. Even when overall development is not phased, it may be
desirable to implement the security aspects of the system over time. For
example, if the controls are expensive or complicated, they may be acquired and
implemented gradually. Similarly, procedural controls may require staff training
to ensure that everyone understands and accepts the reason for the control.
The plan should specify the
order in which the controls are to be implemented so that the most serious
exposures are covered as soon as possible. A timetable also gives milestones by
which to judge the progress of the security program.
Furthermore, the plan must be
extensible. Conditions will change: New equipment will be acquired, new degrees
and modes of connectivity will be requested, and new threats will be
identified. The plan must include a procedure for change and growth, so that
the security aspects of changes are considered as a part of preparing for the
change, not for adding security after the change has been made. The plan should
also contain a schedule for periodic review. Even though there may have been no
obvious, major growth, most organizations experience modest change every day.
At some point the cumulative impact of the change is enough to require the plan
to be modified.
7. Continuing Attention
Good intentions are not
enough when it comes to security. We must not only take care in defining
requirements and controls, but we must also find ways for evaluating a system's
security to be sure that the system is as secure as we intend it to be. Thus,
the security plan must call for reviewing the security situation periodically.
As users, data, and equipment change, new exposures may develop. In addition,
the current means of control may become obsolete or ineffective (such as when
faster processor times enable attackers to break an encryption algorithm). The
inventory of objects and the list of controls should periodically be
scrutinized and updated, and risk analysis performed anew. The security plan
should set times for these periodic reviews, based either on calendar time
(such as, review the plan every nine months) or on the nature of system changes
(such as, review the plan after every major system release).
Related Topics