Chapter: Security in Computing : Is There a Security Problem in Computing?
Methods of Defense
Methods of Defense
We investigate the legal and ethical restrictions
on computer -based crime. But unfortunately, computer crime is certain to
continue for the foreseeable future. For this reason, we must look carefully at
controls for preserving confidentiality, integrity, and availability. Sometimes
these controls can prevent or mitigate attacks; other, less powerful methods
can only inform us that security has been compromised, by detecting a breach as
it happens or after it occurs.
Harm occurs when a threat is
realized against a vulnerability. To protect against harm, then, we can
neutralize the threat, close the vulnerability, or both. The possibility for
harm to occur is called risk. We can deal with harm in several ways. We can
seek to
·
prevent it, by blocking the attack or
closing the vulnerability
·
deter it, by making the attack
harder but not impossible
·
deflect it, by making another target
more attractive (or this one less so)
·
detect it, either as it happens or
some time after the fact
·
recover from its effects
Of course, more than one of
these can be done at once. So, for example, we might try to prevent intrusions.
But in case we do not prevent them all, we might install a detection device to
warn of an imminent attack. And we should have in place incident response
procedures to help in the recovery in case an intrusion does succeed.
Controls
To consider the controls or
countermeasures that attempt to prevent exploiting a computing system's vulnerabilities,
we begin by thinking about traditional ways to enhance physical security. In
the Middle Ages, castles and fortresses were built to protect the people and
valuable property inside. The fortress might have had one or more security
characteristics, including
a strong gate or door, to repel invaders
heavy walls to withstand objects thrown or
projected against them
a surrounding moat, to control access
arrow slits, to let archers shoot at
approaching enemies
crenellations to allow inhabitants to lean out
from the roof and pour hot or vile liquids on attackers
a drawbridge to limit access to authorized
people
gatekeepers to verify that only authorized
people and goods could enter
Similarly, today we use a
multipronged approach to protect our homes and offices. We may combine strong
locks on the doors with a burglar alarm, reinforced windows, and even a nosy
neighbor to keep an eye on our valuables. In each case, we select one or more
ways to deter an intruder or attacker, and we base our selection not only on
the value of what we protect but also on the effort we think an attacker or
intruder will expend to get inside.
Computer security has the
same characteristics. We have many controls at our disposal. Some are easier
than others to use or implement. Some are cheaper than others to use or
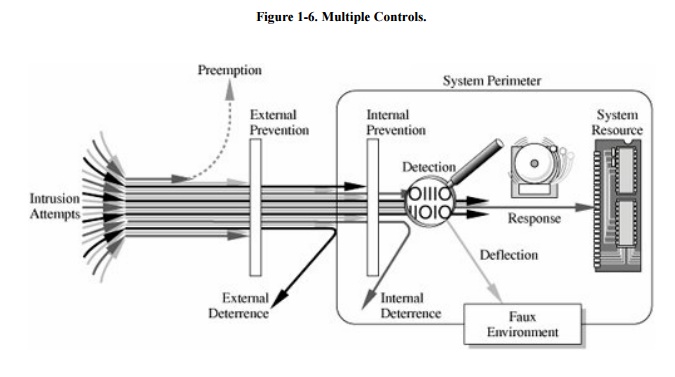
implement. And some are more difficult than others for intruders to override. Figure 1-6 illustrates how we use a combination
of controls to secure our valuable resources. We use one or more controls,
according to what we are protecting, how the cost of protection compares with
the risk of loss, and how hard we think intruders will work to get what they
want.
In this section, we present
an overview of the controls available to us. In later chapters, we examine each
control in much more detail.
Encryption
We noted earlier that we seek
to protect hardware, software, and data. We can make it particularly hard for
an intruder to find data useful if we somehow scramble the data so that interpretation
is meaningless without the intruder's knowing how the scrambling was done.
Indeed, the most powerful tool in providing computer security is this
scrambling or encoding.
Encryption is the formal name for the scrambling process. We take data in their
normal, unscrambled state, called cleartext, and transform them so that they are unintelligible to the outside observer; the
transformed data are called enciphered text or ciphertext. Using encryption,
security professionals can virtually nullify the value of an interception and
the possibility of effective modification or fabrication. In Chapters 2 and 12 we study many ways of devising and applying these
transformations.
Encryption clearly addresses
the need for confidentiality of data. Additionally, it can be used to ensure
integrity; data that cannot be read generally cannot easily be changed in a
meaningful manner. Furthermore, as we see throughout this book, encryption is
the basis of protocols that enable
us to provide security while accomplishing an important system or network task.
A protocol is an agreed-on sequence of
actions that leads to a desired result. For example, some operating system
protocols ensure availability of resources as different tasks and users request
them. Thus, encryption can also be thought of as supporting availability. That
is, encryption is at the heart of methods for ensuring all aspects of computer
security.
Although encryption is an
important tool in any computer security tool kit, we should not overrate its
importance. Encryption does not solve all computer security problems, and other
tools must complement its use. Furthermore, if encryption is not used properly,
it may have no effect on security or could even degrade the performance of the
entire system. Weak encryption can actually be worse than no encryption at all,
because it gives users an unwarranted sense of protection. Therefore, we must
understand those situations in which encryption is most useful as well as ways
to use it effectively.
Software Controls
If encryption is the primary
way of protecting valuables, programs themselves are the second facet of
computer security. Programs must be secure enough to prevent outside attack.
They must also be developed and maintained so that we can be confident of the programs'
dependability.
Program controls include the
following:
internal program controls: parts of the program
that enforce security restrictions, such as access limitations in a database
management program
operating system and network system controls: limitations
enforced by the operating system or network to protect each user from all other
users
independent control programs: application
programs, such as password checkers, intrusion detection utilities, or virus
scanners, that protect against certain types of vulnerabilities
development controls: quality standards under
which a program is designed, coded, tested, and maintained to prevent software
faults from becoming exploitable vulnerabilities
We can implement software
controls by using tools and techniques such as hardware components, encryption,
or information gathering. Software controls frequently affect users directly,
such as when the user is interrupted and asked for a password before being
given access to a program or data. For this reason, we often think of software
controls when we think of how systems have been made secure in the past.
Because they influence the way users interact with a computing system, software
controls must be carefully designed. Ease of use and potency are often competing
goals in the design of a collection of software controls.
Hardware Controls
Numerous hardware devices
have been created to assist in providing computer security. These devices
include a variety of means, such as
·
hardware or smart card implementations of encryption
·
locks or cables limiting access or deterring theft
·
devices to verify users' identities
·
firewalls
·
intrusion detection systems
·
circuit boards that control access to storage media
Policies and Procedures
Sometimes, we can rely on
agreed-on procedures or policies among users rather than enforcing security
through hardware or software means. In fact, some of the simplest controls,
such as frequent changes of passwords, can be achieved at essentially no cost
but with tremendous effect. Training and administration follow immediately
after establishment of policies, to reinforce the importance of security policy
and to ensure their proper use.
We must not forget the value
of community standards and expectations when we consider how to enforce
security. There are many acts that most thoughtful people would consider
harmful, and we can leverage this commonality of belief in our policies. For
this reason, legal and ethical controls are an important part of computer
security. However, the law is slow to evolve, and the technology involving
computers has emerged relatively suddenly. Although legal protection is
necessary and desirable, it may not be as dependable in this area as it would
be when applied to more well-understood and long-standing crimes.
Society in general and the
computing community in particular have not adopted formal standards of ethical
behavior. As we see in Chapter 11, some organizations
have devised codes of ethics for computer professionals. However, before codes
of ethics can become widely accepted and effective, the computing community and the
general public must discuss and make clear what kinds of behavior are
inappropriate and why.
Physical Controls
Some of the easiest, most
effective, and least expensive controls are physical controls. Physical
controls include locks on doors, guards at entry points, backup copies of
important software and data, and physical site planning that reduces the risk
of natural disasters. Often the simple physical controls are overlooked while
we seek more sophisticated approaches.
Effectiveness of Controls
Merely having controls does
no good unless they are used properly. Let us consider several aspects that can
enhance the effectiveness of controls.
Awareness of Problem
People using controls must be
convinced of the need for security. That is, people will willingly cooperate
with security requirements only if they understand why security is appropriate
in a given situation. However, many users are unaware of the need for security,
especially in situations in which a group has recently undertaken a computing
task that was previously performed with lax or no apparent security.
Likelihood of Use
Of course, no control is
effective unless it is used. The lock on a computer room door does no good if
people block the door open. As Sidebar 1-7 tells, some computer
systems are seriously uncontrolled.
Principle of Effectiveness: Controls must be usedand used properlyto be
effective. They must be efficient, easy to use, and appropriate.
This principle implies that
computer security controls must be efficient enough, in terms of time, memory
space, human activity, or other resources used, that using the control does not
seriously affect the task being protected. Controls should be selective so that
they do not exclude legitimate accesses.
Sidebar 1-7: Barn Door Wide Open
In 2001, Wilshire Associates, Inc., a Santa Monica, California-based
investment company that manages about $10 billion of other people's money,
found that its e-mail system had been operating for months with little
security. Outsiders potentially had access to internal messages containing
confidential information about clients and their investments, as well as
sensitive company information.
According to a Washington Post article [OHA01], Wilshire had
hired an outside security investigator in 1999 to review the security of its
system. Thomas Stevens, a senior managing director of Wilshire said, "We
had a report back that said our firewall is like Swiss cheese. We plugged the
holes. We didn't plug all of them." Company officials were "not
overly concerned" about that report because they are "not in the
defense business." In 2001, security analyst George Imburgia checked the
system's security on his own, from the outside (with the same limited knowledge
an attacker would have) and found it was "configured to be available to
everyone; all you need to do is ask."
Wilshire's system enabled employees to access their e-mail remotely. A
senior Wilshire director suggested that the e-mail messages in the system
should have been encrypted.
Overlapping Controls
As we have seen with fortress
or home security, several different controls may apply to address a single
vulnerability. For example, we may choose to implement security for a
microcomputer application by using a combination of controls on program access
to the data, on physical access to the microcomputer and storage media, and
even by file locking to control access to the processing programs.
Periodic Review
Few controls are permanently
effective. Just when the security specialist finds a way to secure assets
against certain kinds of attacks, the opposition doubles its efforts in an
attempt to defeat the security mechanisms. Thus, judging the effectiveness of a
control is an ongoing task. (Sidebar 1-8
reports on periodic reviews of computer security.)
Seldom, if ever, are controls
perfectly effective. Controls fail, controls are incomplete, or people
circumvent or misuse controls, for example. For that reason, we use overlapping controls, sometimes called
a layered defense, in the
expectation that one control will compensate for a failure of another. In some
cases, controls do nicely complement each other. But two controls are not
always better than one and, in some cases, two can even be worse than one. This
brings us to another security principle.
Principle of Weakest Link: Security can be no stronger than its weakest
link. Whether it is the power supply that powers the firewall or the operating system under the security
application or the human who plans, implements, and administers controls, a
failure of any control can lead to a security failure.
Sidebar 1-8: U.S. Government's
Computer Security Report Card
The U.S. Congress requires government agencies to supply annual reports
to the Office of Management and Budget (OMB) on the state of computer security
in the agencies. The agencies must report efforts to protect their computer
networks against crackers, terrorists, and other attackers.
In November 2001, for the third edition of this book, two-thirds of the
government agencies received a grade of F (the lowest possible) on the computer
security report card based on the OMB data. The good news for this edition is
that in 2005 only 8 of 24 agencies received grades of F and 7 agencies received
a grade of A. The bad, and certainly sad, news is that the average grade was
D+. Also disturbing is that the grades of 7 agencies fell from 2004 to 2005.
Among the failing agencies were Defense, State, Homeland Security, and Veterans
Affairs. The Treasury Department received a D-. A grades went to Labor, Social
Security Administration, and the National Science Foundation, among others.
(Source: U.S. House of Representatives Government Reform Committee.)
Related Topics