Chapter: Information Security : Physical Design
Information Security: Access Control Devices
ACCESS CONTROL DEVICES
Successful
access control system includes number of components, depending on system’s
needs for authentication and authorization
Strong
authentication requires at least two forms of authentication to authenticate
the supplicant’s identity
The
technology to manage authentication based on what a supplicant knows is widely
integrated into the networking and security software systems in use across the
IT industry
Authentication
Authentication is validation of a supplicant’s identity
Four general ways in which authentication is carried out:
What a supplicant knows
What a supplicant has
Who a supplicant is
What a supplicant produces
Authorization: Are you allowed to do that?
Enforces
limits on actions
Note: Access control often used as synonym for authorization
Authentication
How to authenticate a human to a machine?
Can be based on…
Something you know
For
example, a password
Something you have
For
example, a smartcard
Something you are
For example, your fingerprint
Passwords
Lots of things act as passwords!
PIN
Social security number
Mother’s maiden name
Date of birth
Name of your pet, etc.
Trouble with Passwords
“Passwords
are one of the biggest practical problems facing security engineers today.”
“Humans are
incapable of securely storing high-quality cryptographic keys, and they have
unacceptable speed and accuracy when performing cryptographic operations. (They
are also large, expensive to maintain, difficult to manage, and they pollute
the environment. It is astonishing that these devices continue to be
manufactured and deployed.)”
Why Passwords?
Why is
“something you know” more popular than “something you have” and “something you
are”?
Cost: passwords are free
Convenience: easier for SA to reset pwd than
to issue user a new thumb
Keys vs Passwords
Crypto keys
Spse key is 64 bits
Then 264 keys
Choose key at random
Then
attacker must try about 263 keys
Spse passwords are 8 characters, and 256 different characters
Then 2568 = 264 pwds
Users do not select passwords
at random
Attacker has far less than 263 pwds to try (dictionary attack)
Good and Bad Passwords
Bad passwords
frank
Fido
password
4444
Pikachu
102560
Good Passwords?
jfIej,43j-EmmL+y
09864376537263
P0kem0N
FSa7Yago
0nceuP0nAt1m8
Password Experiment
Three groups of users ¾ each
group advised to select passwords as follows
Group A: At least
6 chars, 1 non-letter
Group B: Password
based on passphrase
Group C: 8 random
characters
Results
Group A: About 30% of pwds easy to crack
Group B: About 10% cracked
Passwords
easy to remember
Group C:
About 10% cracked
Passwords
hard to remember
User compliance hard to achieve
In each case, 1/3rd did not comply (and about 1/3rd of those easy to
crack!)
Assigned passwords sometimes best
If passwords not assigned, best advice is
Choose passwords based on passphrase
Use pwd cracking tool to test for weak pwds
Require periodic password changes?
Attacks on Passwords
Attacker could…
Target one particular account
Target any account on system
Target any account on any system
Attempt denial of service (DoS) attack
Common
attack path
Outsider ® normal
user ® administrator
May only require one weak password!
Password Retry
Suppose
system locks after 3 bad passwords. How long should it lock?
5 seconds
5 minutes
Until SA restores service
What are +’s and -’s of each?
Password File
Bad idea to store passwords in a file
But need a way to verify passwords
Cryptographic solution: hash the passwords
Store y = h(password)
Can verify entered password by hashing
If attacker obtains password file, he does
not obtain passwords
But
attacker with password file can guess x and check whether y = h(x)
If so, attacker has found password!
Dictionary Attack
Attacker pre-computes h(x) for all x in a dictionary of common passwords
Suppose attacker gets access to password file containing hashed
passwords
Attacker only needs to compare hashes to his
pre-computed dictionary
Same attack will work each time
Can we prevent this attack? Or at least make attacker’s job more
difficult?
Password Cracking:Do the Math
Assumptions
Pwds are 8 chars, 128 choices per character
Then 1288 = 256 possible
passwords
There is a password file with
210 pwds
Attacker has dictionary of 220
common pwds
Probability of 1/4 that a pwd is in dictionary
Work is
measured by number of hashes
Password Cracking
Must try 256/2 = 255 on average
Just like exhaustive key search
Attack 1 password with dictionary
Expected work is about
But in practice, try all in dictionary and quit if not found work is at most 220 and probability of success is 1/4
Attack any of 1024 passwords in file
Without dictionary
Assume all 210 passwords are distinct
Need 255 comparisons before expect to
find password
If no salt, each hash computation gives 210
comparisons Þ the expected work (number of
hashes) is 255/210 = 245
If salt is used, expected work is 255
since each comparison requires a new hash computation
Attack any of 1024 passwords in file
With dictionary
Probability at least one password is in dictionary
is 1 - (3/4)1024 = 1
We ignore case where no pwd is in dictionary
If no salt, work is about 219/210
= 29
If salt, expected work is less than 222
Note: If no salt, we can precompute all
dictionary hashes and amortize the work
Password cracking is too easy!
One weak
password may break security
Users
choose bad passwords
Social
engineering attacks, etc.
The bad
guy has all of the advantages
All of
the math favors bad guys
Passwords
are a big security problem
Password Cracking Tools
Popular
password cracking tools
Password
Crackers
Password
Portal
L0phtCrack
and LC4 (Windows)
John the
Ripper (Unix)
Admins
should use these tools to test for weak passwords since attackers will!
Good
article on password cracking
Passwords
- Conerstone of Computer Security
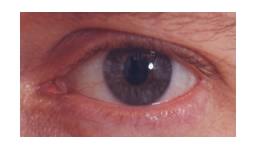
Biometric
“You are your key” ¾ Schneier
Examples
Fingerprint
Handwritten signature
Facial recognition
Speech recognition
Gait (walking) recognition
“Digital doggie” (odor recognition)
Many more!
Why Biometrics?
Biometrics seen as desirable replacement for passwords
Cheap and reliable biometrics needed
Today, a very active area of research
Biometrics are used in security today
Thumbprint mouse
Palm print for secure entry
Fingerprint to unlock car door, etc.
But biometrics not too popular
Has not lived up to its promise (yet)
Ideal Biometric
Universal ¾ applies
to (almost) everyone
In reality, no biometric applies to everyone
Distinguishing ¾ distinguish
with certainty
In reality, cannot hope for 100% certainty
Permanent ¾ physical
characteristic being measured never changes
In reality, want it to remain valid for a long time
Collectable ¾ easy to
collect required data
Depends on whether subjects are cooperative
Safe, easy to use, etc., etc.
Biometric Modes
ü Identification
¾ Who goes
there?
Compare
one to many
Example:
The FBI fingerprint database
Authentication
Is that really you?
Compare
one to one
Example:
Thumbprint mouse
Identification
problem more difficult
More
“random” matches since more comparisons
Fingerprint
Comparison
Examples
of loops, whorls and arches
Minutia
extracted from these features
Related Topics