Chapter: Cryptography and Network Security Principles and Practice : One Symmetric Ciphers : Classical Encryption Techniques
Transposition Techniques
TRANSPOSITION
TECHNIQUES
All the
techniques examined so far involve the substitution of a ciphertext symbol for
a plaintext symbol. A very different kind of mapping is achieved by performing
some sort of permutation on the plaintext letters. This technique is referred
to as a transposition cipher.
The
simplest such cipher is the rail fence technique, in which the plaintext
is written down as a sequence of diagonals and then read off as a sequence of
rows. For example, to encipher the message “meet me after the toga party” with
a rail fence of depth 2, we write the following:
m e m a t r h t g p r y
e t e f e t e o a a t
The encrypted message is
MEMATRHTGPRYETEFETEOAAT
This sort of thing would be trivial to
cryptanalyze. A more complex scheme is to write the message in a rectangle, row
by row, and read the message off, column by column, but permute the order of
the columns. The order of the columns then becomes the key to the algorithm.
For example,
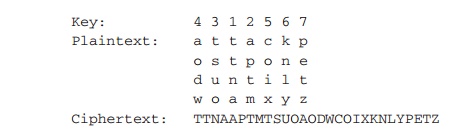
Thus, in this example, the key is
4312567. To encrypt, start with the column that is labeled 1, in this case
column 3. Write down all the letters in that column. Proceed to column 4, which
is labeled 2, then column 2, then column 1, then columns 5, 6, and 7.
A pure transposition cipher is easily
recognized because it has the same letter frequencies as the original
plaintext. For the type of columnar transposition just shown, cryptanalysis is
fairly straightforward and involves laying out the ciphertext in a matrix and
playing around with column positions. Digram and trigram frequency tables can
be useful.
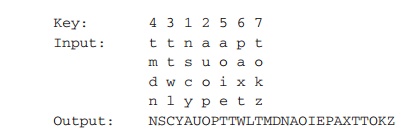
The transposition cipher can be made significantly more secure
by performing more than one stage of transposition. The result is a more
complex permutation that is not easily reconstructed. Thus, if the foregoing
message is reencrypted using the same algorithm,
To visualize the result of this double
transposition, designate the letters in the original plaintext message by the
numbers designating their position. Thus, with 28 letters in the message, the
original sequence of letters is
01 02 03 04 05 06 07 08 09 10 11 12 13 14
15 16 17 18 19 20 21 22 23 24 25 26 27 28
After the first transposition, we have
03 10 17 24 04 11 18 25 02 09 16 23 01 08
15 22 05 12 19 26 06 13 20 27 07 14 21 28
which has a somewhat regular structure. But after the second
transposition, we have
17 09 05 27 24 16 12 07 10 02 22 20 03 25
15 13 04 23 19 14 11 01 26 21 18 08 06 28
This is a much less structured permutation and is much more
difficult to cryptanalyze.
Related Topics