Chapter: Cryptography and Network Security Principles and Practice : Network and Internet Security : IP Security
IP Security Overview
IP SECURITY OVERVIEW
In 1994, the Internet Architecture Board
(IAB) issued a report titled “Security in the Internet Architecture” (RFC
1636). The report identified key areas for security mechanisms.
Among these were
the need to
secure the network infrastructure
from unauthorized monitoring and control of network traffic and the need to
secure end-user-to-end-user traffic using authentication and encryption
mechanisms.
To provide security, the IAB included
authentication and encryption as necessary security features in the
next-generation IP, which has been issued as IPv6. Fortunately, these security
capabilities were designed to be usable both with the current IPv4 and the future
IPv6. This means that vendors can begin offering these features now, and many
vendors now do have some IPsec capabil- ity in their products. The IPsec
specification now exists as a set of Internet standards.
Applications of IPsec
IPsec provides the
capability to secure
communications across a LAN, across private and public WANs, and across
the Internet. Examples
of its use include:
•
Secure branch office
connectivity over the
Internet: A company can
build a secure virtual
private network over the Internet or over a public WAN. This enables a business to rely heavily on the Internet and
reduce its need for private
networks, saving costs and network
management overhead.
•
Secure remote access
over the Internet: An end
user whose system
is equipped with IP security protocols
can make a local call to an Internet Service
Provider (ISP) and gain secure access
to a company network. This reduces
the cost of toll
charges for traveling employees and telecommuters.
•
Establishing extranet and intranet connectivity with partners: IPsec can be used to secure communication with other
organizations, ensuring authentica- tion and confidentiality and providing a
key exchange mechanism.
•
Enhancing electronic commerce security: Even though some Web and electronic commerce applications have built-in security protocols, the use
of IPsec enhances that security. IPsec guarantees that all traffic
designated by the network adminis-
trator is both encrypted and authenticated, adding an additional layer of security to whatever is provided
at the application layer.
The principal feature of IPsec that enables it to support these varied
applica- tions is that it can encrypt and/or
authenticate all traffic at the IP level. Thus, all dis-
tributed applications (including remote logon, client/server, e-mail, file transfer, Web access,
and so on) can be secured.
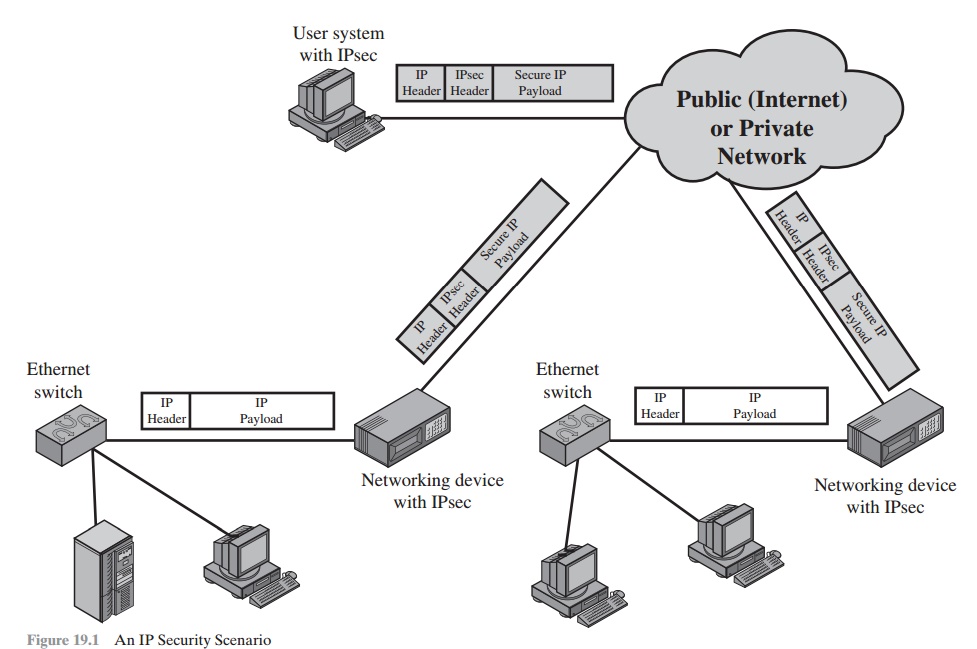
Figure 19.1
is a typical scenario of IPsec usage. An organization maintains LANs
at dispersed locations. Nonsecure IP traffic is conducted on each LAN. For traffic offsite, through some sort of private or public WAN, IPsec
protocols are used. These protocols operate in networking devices,
such as a router or firewall, that con-
nect each LAN to the outside world. The IPsec networking device will typically
encrypt and compress all traffic going into the WAN and decrypt and decompress traffic coming from the WAN; these operations are transparent to workstations and servers on the LAN. Secure
transmission is also possible with individual users
who dial into the WAN. Such
user workstations must implement the IPsec protocols to provide security.
Benefits of IPsec
Some of the benefits of IPsec:
•
When IPsec is implemented in a firewall
or router, it provides
strong security that can be applied
to all traffic crossing the perimeter. Traffic within
a company or workgroup does not incur
the overhead of security-related processing.
•
IPsec in a firewall
is resistant to bypass if all traffic
from the outside
must use IP and the firewall
is the only means of entrance from the Internet into the organization.
•
IPsec
is below the transport
layer (TCP, UDP) and so is
transparent to applications. There is no need to change software on a user or server system when
IPsec is implemented in the firewall or
router. Even if IPsec
is implemented in end systems, upper-layer software, including
applications, is not affected.
•
IPsec can be transparent to end users. There is no need to train
users on security mechanisms, issue keying
material on a per-user
basis, or revoke keying
material when users leave
the organization.
•
IPsec can
provide security for
individual users if needed. This is useful for
offsite workers and for setting up a secure virtual subnetwork within an organization
for sensitive applications.
Routing Applications
In addition to supporting end users and protecting premises
systems and networks, IPsec can play a vital role in
the routing architecture required for internetworking.
[HUIT98] lists the following examples
of the use of IPsec.
IPsec can assure that
•
A router
advertisement (a new router advertises its presence) comes from an authorized router.
•
A neighbor
advertisement (a router seeks to establish or maintain a neighbor relationship
with a router in another routing domain) comes from an autho- rized router.
•
A redirect message comes from the router
to which the initial IP packet
was sent.
•
A routing update is
not forged.
Without such security measures,
an opponent can disrupt communications
or divert some traffic. Routing protocols such as Open Shortest Path
First (OSPF) should be run on top
of security associations between
routers that are defined by
IPsec.
IPsec Documents
IPsec encompasses three functional areas:
authentication, confidentiality, and key management. The totality of the IPsec
specification is scattered across dozens of RFCs and draft IETF
documents, making this
the most complex
and difficult to grasp
of all IETF specifications. The best way to grasp the scope of IPsec is to consult
the latest version of the IPsec
document roadmap, which
as of this writing is [FRAN09].
The
documents can be categorized into
the following groups.
•
Architecture: Covers the general
concepts, security requirements, definitions, and mechanisms defining IPsec
technology. The current
specification is RFC 4301, Security Architecture for the Internet
Protocol.
•
Authentication Header (AH): AH is an extension header
to provide message authentication.
The current specification is RFC 4302,
IP Authentication Header. Because message
authentication is provided
by ESP, the use of AH is
deprecated. It is included in IPsecv3 for backward compatibility but should not be used in new applications. We do not discuss
AH in this chapter.
•
Encapsulating Security Payload (ESP): ESP consists
of an encapsulating header
and trailer used to provide encryption or combined encryption/authentication. The current
specification is RFC 4303, IP Encapsulating Security Payload (ESP).
•
Internet Key Exchange
(IKE): This is a collection of documents describing the key
management schemes for use with IPsec. The main specification is RFC 4306, Internet
Key Exchange (IKEv2) Protocol,
but there are a number of related RFCs.
•
Cryptographic algorithms: This category
encompasses a large set of docu- ments that define and describe cryptographic algorithms for encryption, mes- sage authentication, pseudorandom functions (PRFs), and
cryptographic key exchange.
•
Other: There are a variety of other IPsec-related RFCs, including those deal- ing with security policy
and management information base (MIB) content.
IPsec Services
IPsec provides security
services at the IP layer by enabling a system to select required security
protocols, determine the algorithm(s) to use for the service(s), and put in place
any cryptographic keys required to provide the requested services. Two protocols are used to provide security:
an authentication protocol
designated by the header of the protocol, Authentication
Header (AH); and a combined encryption/ authentication protocol designated by
the format of the packet for that protocol, Encapsulating Security
Payload (ESP). RFC 4301 lists
the following services:
•
Access control
•
Connectionless integrity
•
Data origin authentication
•
Rejection of replayed packets
(a form of partial sequence
integrity)
•
Confidentiality (encryption)
•
Limited traffic flow confidentiality
Transport and Tunnel Modes
Both AH and ESP support
two modes of use: transport
and tunnel mode.
The oper- ation of these two modes is best understood in the
context of a description of ESP, which
is covered in Section 19.3.
Here we provide
a brief overview.
TRANSPORT MODE Transport mode provides protection primarily for
upper-layer protocols. That is, transport mode protection extends to the payload
of an IP packet.1 Examples include a TCP or UDP segment
or an ICMP packet, all of which operate directly above IP in a host protocol
stack. Typically, transport mode is used
for end-to-end communication between two hosts
(e.g., a client and a server,
or two workstations). When a host runs AH or ESP over IPv4, the payload
is the data that normally follow
the IP header. For IPv6, the payload is the data that normally
follow both the IP header
and any IPv6 extensions headers that are
present, with the possible
exception of the destination options
header, which may be included in the protection.
ESP in transport mode encrypts and
optionally authenticates the IP payload but not the IP header. AH in transport
mode authenticates the IP payload and selected portions of the IP header.
TUNNEL MODE Tunnel mode provides protection to the entire IP packet. To
achieve this, after the
AH or ESP fields are
added to the IP packet,
the entire packet plus security fields is treated as the payload of
new outer IP packet with a new outer IP
header. The entire original, inner, packet travels through a tunnel from one point of an IP network to
another; no routers along the way are able to examine the inner IP header.
Because the original packet is encapsulated,
the new, larger packet may
have totally different source and destination addresses, adding to the security. Tunnel mode is used when one or both ends of a security
association (SA) are a security gateway, such as a firewall or router
that implements IPsec. With tunnel mode, a number of hosts on networks behind
firewalls may engage in secure communications without implementing IPsec. The unprotected packets generated
by such hosts are tunneled through external networks by tunnel mode SAs set up by the IPsec software in the firewall
or secure router at the boundary of the local network.
Here is an example of how tunnel
mode IPsec operates. Host A on a network generates an IP packet with the
destination address of host B on another network. This packet is routed from
the originating host to a firewall or secure router at the boundary of A’s network. The firewall filters
all outgoing packets
to determine the need for IPsec processing. If this
packet from A to B requires IPsec, the firewall performs IPsec processing and encapsulates the packet with an outer
IP header. The source IP address of this outer IP packet is this firewall, and the destination address may be a firewall that forms the boundary to B’s local
network. This packet
is now routed to B’s firewall, with intermediate routers examining only the outer
IP header. At B’s firewall, the
outer IP header is stripped off, and
the inner packet is delivered to B.
ESP in tunnel mode encrypts and optionally
authenticates the entire inner IP packet, including the inner IP header. AH in
tunnel mode authenticates the entire inner IP packet and selected portions of
the outer IP header.
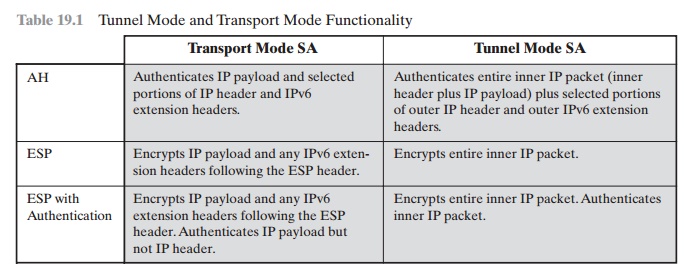
Table 19.1 summarizes transport and tunnel
mode functionality.
Related Topics