Chapter: 11th Computer Science : Chapter 17 : Computer Ethics and Cyber Security
Computer Ethical Issues
ETHICAL
ISSUES
An
Ethical issue is a problem or issue that requires a person or organization to
choose between alternatives that must be evaluated as right (ethical) or wrong
(unethical). These issues must be addressed and resolved to have a positive
influence in society.
Some
of the common ethical issues are listed below:
•
Cyber crime
•
Software Piracy
•
Unauthorized Access
•
Hacking
•
Use of computers to commit fraud
•
Sabotage in the form of viruses
•
Making false claims using computers
CYBER CRIME
Cybercrime
is an intellectual, white-collar crime. Those who commit such crimes generally
manipulate the computer system in an intelligent manner.
For
example – illegal money transferviainternet.
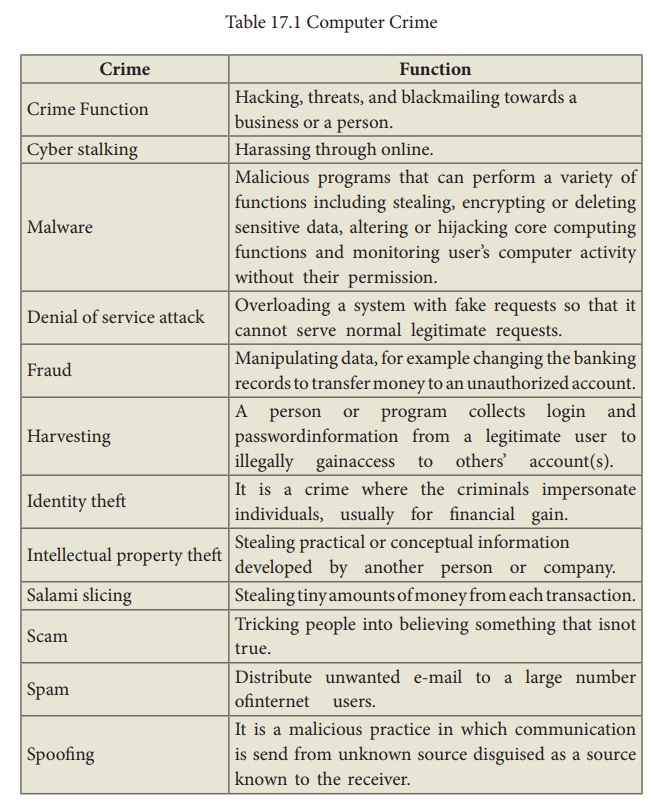
Examples
of some Computer crimes and their functions are listed below in Table 17.1:
SOFTWARE PIRACY
Software
Piracy is about the copyright violation of software created originally by an
individual or an institution. It includes stealing of codes / programs and
other information illegally and creating duplicate copies by unauthorized means
and utilizing this data either for one’s own benefit or for commercial profit.
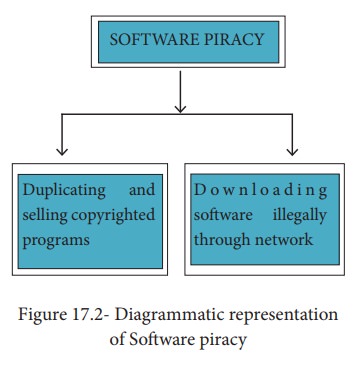
In
simple words,Software Piracy is “unauthorized copying of software”. Figure 17.2 shows a diagrammatical representation of software piracy.
Most
of the commercial software is licensed for use at a single computer site or for
use by only one user at any time. When a user buys any software, he becomes a
licensed user for that software. He is allowed to make copies of the program
for backup purposes, but it is against the law to distribute duplicate copies
to others. Such illegal copying and distribution of commercial software should
not be practiced.
An entirely different approach to software piracy is called shareware, acknowledges the futility of trying to stop people from copying software and instead relies on people’s honesty. Shareware publishers encourage users to give copies of programs to friends and colleagues but ask everyone who uses that program regularly to pay a registration fee to the program’s author directly. Commercial programs that are made available to the public illegally are often called warez.
UNAUTHORIZED ACCESS
Unauthorized
access is when someone gains access to a website, program, server, service, or
other system by breaking into a legitimate user account. For example, if
someone tries guessing a password or username for an account that was not
theirs until they gained access, it is considered an unauthorized access.
To
prevent unauthorized access, Firewalls, Intrusion
Detection Systems (IDS), Virus and Content Scanners, Patches and Hot fixes
are used.
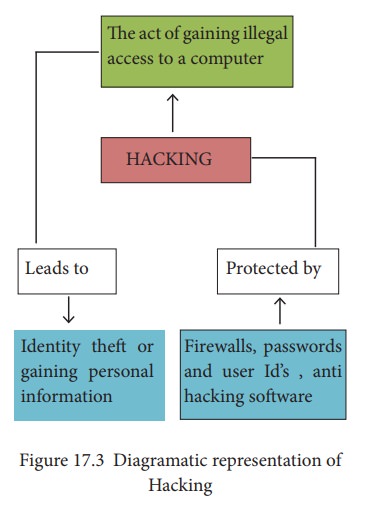
HACKING
Hacking
is intruding into a computer system to steal personal data without the owner’s
permission or knowledge (liketo steal a password). It is also gaining
unauthorized access to a computer system, and altering its contents. It may be
done in pursuit of a criminal activity or it may be a hobby. Hacking may be
harmless if the hacker is only enjoying the challenge of breaking systems’
defenses, but such ethical hacking should be practiced only as controlled
experiments. Figure 17.3 shows a
diagrammatic representation of Hacking.
CRACKING
Cracking
is where someone edits a program source so that the code can be exploited or
modified. A cracker (also called a black hat or dark side hacker) is a
malicious or criminal hacker. “Cracking” means trying to get into computer
systems in order to steal, corrupt, or illegitimately view data.
A
cracker is someone who breaks into someone else's computer system, often on a
network, bypassing passwords or licenses in computer programs.
Software
cracking is the most often used type of cracking which is nothing but removing
the encoded copy protection. There is another type of cracking called password
cracking. This is mainly used to crack the passwords. Password cracking can be
perform either by using an automated program or can be manually realized.
![]() One more interesting fact about cracking is social
engineering. It is a method of getting passwords and information using human
weakness. These crackers trick people, not software. They can use just the
phone for getting information, they can pretend being your friend and talk to
you on Internet Relay Chat(IRC) or
by Instant messenger. e-mail can also be a source for them. They may send
official e-mail requesting some sensitive information. It may look like a
legitimate e-mail from bank or other official institution.
One more interesting fact about cracking is social
engineering. It is a method of getting passwords and information using human
weakness. These crackers trick people, not software. They can use just the
phone for getting information, they can pretend being your friend and talk to
you on Internet Relay Chat(IRC) or
by Instant messenger. e-mail can also be a source for them. They may send
official e-mail requesting some sensitive information. It may look like a
legitimate e-mail from bank or other official institution.
The
other method that uses social engineering crackers is password guessing. They
find your personal information from some personal data/facts and try to guess a
password.
Usually
a cracker maintains knowledge of the vulnerabilities he or she finds and
exploits them for personal advantage, not revealing them to either to the
general public or to the manufacturer.
Related Topics