Chapter: Web Technology : Web Essentials
Web Essentials
Web Essentials:
Server:
The
software that distributes the information and the machine where the information
and software reside is called the server.
• provides
requested service to client
• e.g., Web
server sends requested Web page
Client:
The
software that resides on the remote machine, communicates with the server,
fetches the information, processes it, and then displays it on the remote
machine is called the client.
• initiates
contact with server (“speaks first”)
• typically
requests service from server
• Web:
client implemented in browser
Web
server:
Software
that delivers Web pages and other documents to browsers using the HTTP protocol
Web Page:
A web
page is a document or resource of information that is suitable for the World
Wide Web and can be accessed through a web browser.
Website:
A
collection of pages on the World Wide Web that are accessible from the same URL
and typically residing on the same server.
URL:
Uniform Resource
Locator, the unique address which identifies a resource on the Internet for
routing purposes.
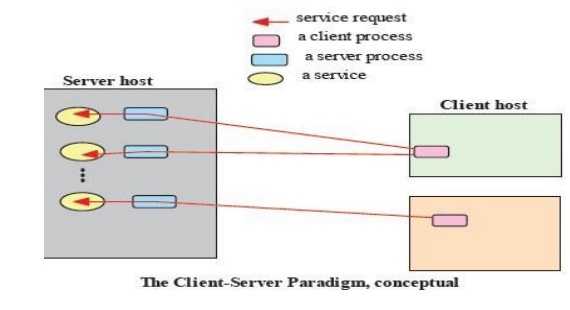
Client-server paradigm:
The
Client-Server paradigm is the most prevalent model for distributed computing
protocols. It is the basis of all distributed computing paradigms at a higher
level of abstraction. It is service-oriented, and employs a request-response
protocol.
A server
process, running on a server host, provides access to a service. A client
process, running on a client host, accesses the service via the server
process.The interaction of the process proceeds according to a protocol.
The
primary idea of a client/server system is that you have a central repository of
information—some kind of data, often in a database—that you want to distribute
on demand to some set of people or machines.
The Internet:
• Medium
for communication and interaction in inter connected network.
• Makes
information constantly and instantly available to anyone with a connection.
Web Browsers:
• User agent for Web is called a browser: o
Internet Explorer
o Firefox
Web Server:
• Server for Web is called Web server: o Apache
(public domain)
o MS
Internet Information Server
Protocol:
Protocols are agreed formats for transmitting data
between devices. The protocol determines:
i. The error
checking required
ii. Data
compression method used
iii. The way
the end of a message is signaled
iv. The way
the device indicates that it has received the message
Internet Protocol:
There are many protocols used by the Internet and
the WWW:
o TCP/IP
o HTTP
o FTP
o
Electronic mail protocols IMAP
o POP
TCP/IP
The
Internet uses two main protocols (developed by Vincent Cerf and Robert Kahn)
Transmission control protocol (TCP):Controls disassembly of message into
packets at the origin reassembles at the destination
Internet
protocol (IP):Specifies the addressing details for each packet Each packet is
labelled with its origin and destination.
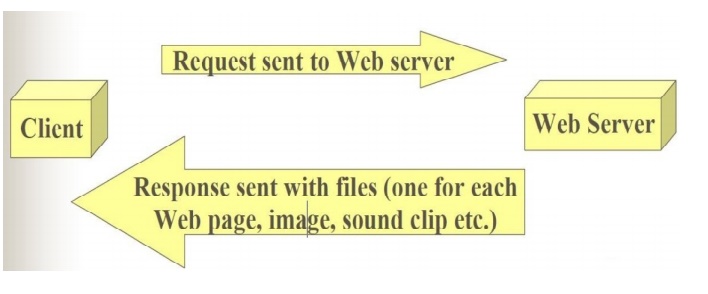
Hypertext Transfer Protocol
(HTTP)
• The hypertext transfer protocol (HTTP) was developed by Tim
Berners-Lee in 1991
• HTTP was designed to transfer pages between machines
• The client (or Web browser) makes a request for a given page and the Server is responsible for finding it and returning it to the client
• The
browser connects and requests a page from the server
• The
server reads the page from the file system, sends it to the client and
terminates the connection.
Electronic Mail Protocols:
• Electronic
mail uses the client/server model
• The
organisation has an email server devoted to handling email o Stores and
forwards email messages
• Individuals
use email client software to read and send email
o (e.g.
Microsoft Outlook, or Netscape Messenger)
• Simple
Mail Transfer Protocol (SMTP)
o
Specifies format of mail messages
• Post
Office Protocol (POP) tells the email server to:
o Send
mail to the user’s computer and delete it from the server
o Send
mail to the user’s computer and do not delete it from the server o Ask whether
new mail has arrived.
Interactive Mail Access Protocol
(IMAP)
Newer
than POP, provides similar functions with additional features.
o e.g. can send specific messages to the client
rather than all the messages. A user can view email message headers and the
sender’s name before
downloading
the entire message.
Allows
users to delete and search mailboxes held on the email server.
The disadvantage of POP: You can
only access messages from one PC.
The disadvantage of IMAP :Since
email is stored on the email server, there is a need for more and more expensive (high speed)
storage space.
World Wide Web: comprises software (Web server
and browser) and data (Web sites).
Internet Protocol (IP) Addresses:
- Every
node has a unique numeric address
- Form:
32-bit binary number
- New
standard, IPv6, has 128 bits (1998)
- Organizations
are assigned groups of IPs for their computers
- Domain names
- Form:
host-name. domain-names
- First
domain is the smallest (Google)
- Last
domain specifies the type of organization (.com)
- Fully
qualified domain name - the host name and all of the domain names
- DNS
servers - convert fully qualified domain names to IPs
HTTP:
Hypertext
Transfer Protocol (HTTP) is the communication protocol used by the Internet to
transfer hypertext documents.
A
protocol to transfer hypertext requests and information between servers and
browsers
Hypertext
is text, displayed on a computer, with references (hyperlinks) to
other
text that the reader can immediately follow, usually by a mouse HTTP is behind
every request for a web document or graph, every click of a hypertext link, and
every submission of a form.
HTTP
specifies how clients request data,
and how servers respond to these
requests.
The
client makes a request for a given page and the server is responsible for
finding it and returning it to the client.
The
browser connects and requests a page from the server.
The
server reads the page from the file system and sends it to the client and then
terminates the connection
HTTP
Transactions
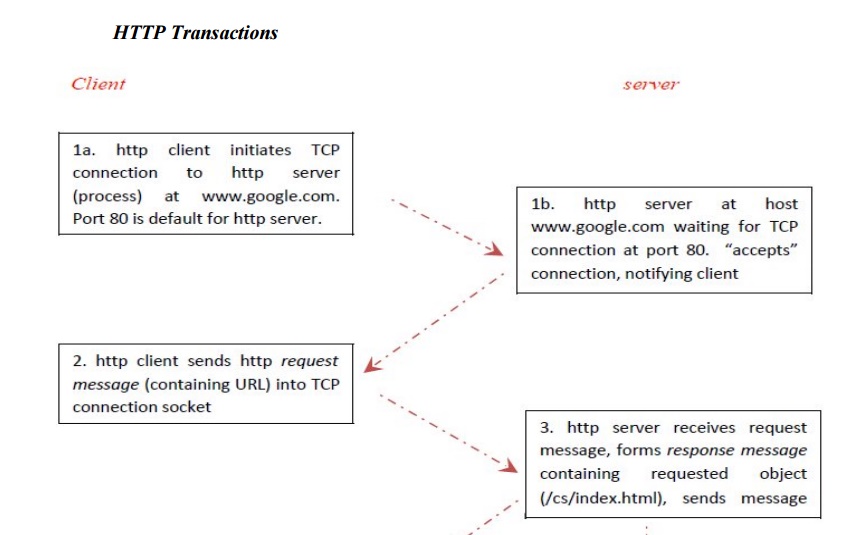
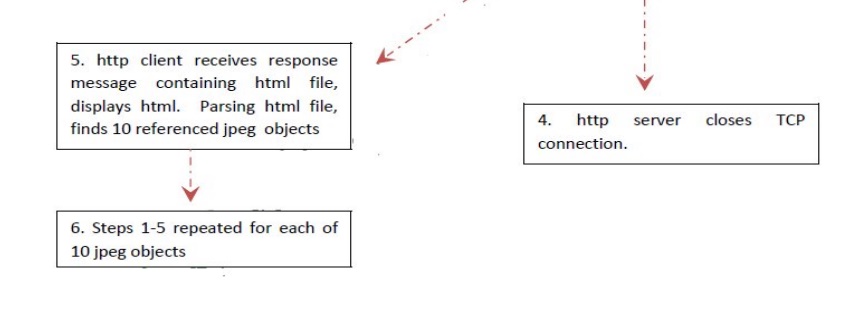
HTTP Message:
HTTP
message is the information transaction between the client and server.
Two types of HTTP Message:
1. Requests
a. Client to
server
2. Responses
a. Server to
client
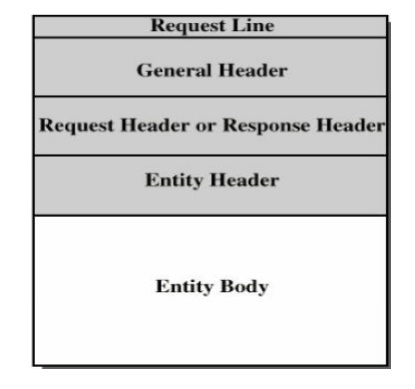
Fields
· Request
line or Response line
· General
header
· Request
header or Response header
· Entity
header
· Entity
body
Request Message:
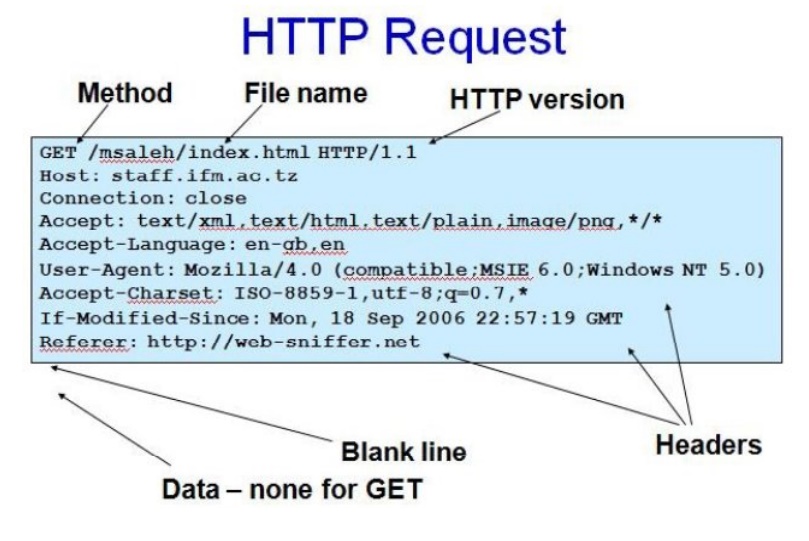
Request Line:
• A request
line has three parts, separated by spaces o a method name
o the
local path of the requested resource o the version of HTTP being used
• A typical
request line is:
o GET
/path/to/file/index.html HTTP/1.1
• Notes:
o GET is the most common HTTP
method; it says "give me this resource". Other methods include POST and HEAD. Method names are always uppercase
o The
path is the part of the URL after the host name, also called the request URI o The HTTP version always
takes the form "HTTP/x.x",
uppercase.
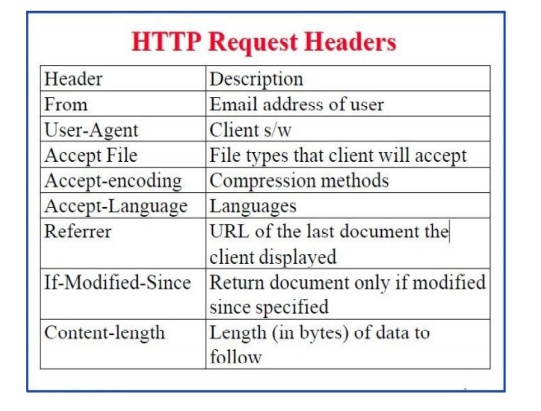
Request Header:
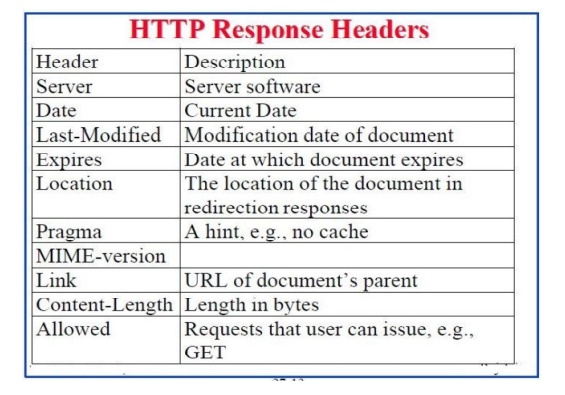
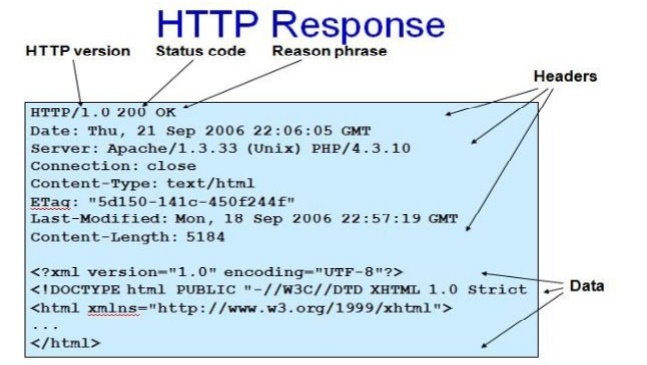
Response
Message:
Response Line:
• A request
line has three parts, separated by spaces o the HTTP version,
o a response status code that gives the
result of the request, and o an English reason
phrase describing the status code
• Typical
status lines are:
o
HTTP/1.0 200 OK or
o
HTTP/1.0 404 Not Found
• Notes:
o The
HTTP version is in the same format as in the request line, "HTTP/x.x".
o The status code is meant to be computer-readable; the reason phrase is
meant to be human-readable, and may vary.
HTTP Request Header:
EXAMPLE
HTTP Method:
• HTTP
method is supplied in the request line and specifies the operation that the
client has requested.
Some common methods:
• Options
• Get
• Head
• Post
• Put
• Move
• Delete
Two methods that are mostly used
are the GET and POST: o GET
for queries that can be safely repeated
o POST for operations that may have side
effects (e.g. ordering a book from an on-line store).
The GET Method
• It is
used to retrieve information from a specified URI and is assumed to be a safe,
repeatable operation by browsers, caches and other HTTP aware components
• Operations
have no side effects and GET requests can be re-issued.
• For
example, displaying the balance of a bank account has no effect on the account
and can be safely repeated.
• Most
browsers will allow a user to refresh a page that resulted from a GET, without displaying any kind of
warning
• Proxies
may automatically retry GET requests
if they encounter a temporary network connection problem.
• GET
requests is that they can only supply data in the form of parameters encoded in
the URI (known as a Query String) –
[downside]
Cannot be
unused for uploading files or other operations that require large amounts of
data to be sent to the server.
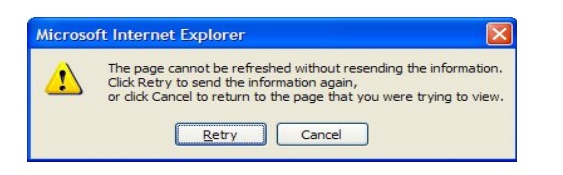
The POST Method
• Used for
operations that have side effects and cannot be safely repeated.
• For
example, transferring money from one bank account to another has side effects
and should not be repeated without explicit approval by the user.
If you
try to refresh a page in Internet Explorer that resulted from a POST, it displays the following message
to warn you that there may be side effects:
The POST
request message has a content body that is normally used to send parameters and
data
• The IIS
server returns two status codes in its response for a POST request
o The
first is 100 Continue to indicate
that it has successfully received the POST
request
o The
second is 200 OK after the request
has been processed.
HTTP response status codes
• Informational
(1xx)
• Successful
(2xx)
• Redirection
(3xx)
o 301:
moved permanently
• Client
error (4xx)
o 403 :
forbidden o 404: Not found
• Server
error (5xx)
o 503:
Service unavailable
o 505:
HTTP version not supported
Related Topics