Chapter: Computer Networks : Transport Layer
Overview of Transport Layer
OVERVIEW OF TRANSPORT LAYER
TCP was specifically designed to provide a reliable end to end byte stream over an unreliable internetwork. Each machine supporting TCP has a TCP transport entity either a user process or part of the kernel that manages TCP streams and interface to IP layer. A TCP entity accepts user data streams from local processes, breaks them up into pieces not exceeding 64KB and sends each piece as a separate IP datagram. Client Server mechanism is not necessary for TCP to behave properly.
The IP
layer gives no guarantee that datagram will be delivered properly, so it is up
to TCP to timeout and retransmit, if needed. Duplicate, lost and out of
sequence packets are handled using the sequence number, acknowledgements,
retransmission, timers, etc to provide a reliable service. Connection is a must
for this service.Bit errors are taken care of by the CRC checksum. One
difference from usual sequence numbering is that each byte is given a number
instead of each packet. This is done so that at the time of transmission in
case of loss, data of many small packets can be combined together to get a
larger packet, and hence smaller overhead.
TCP
connection is a duplex connection.
That means there is no difference between two sides once the connection is
established.
Salient Features of TCP
·
Piggybacking
of Acknowledgments: The ACK for the last received packet need not be sent as a new packet, but gets a free
ride on the next outgoing data frame(using the ACK field in the frame header).
The technique is temporarily delaying outgoing ACKs so that they can be hooked
on the next outgoing data frame is known as piggybacking. But ACK can't be
delayed for a long time if receiver(of the packet to be acknowledged) does not
have any data to send.
·
Flow and
congestion control: TCP takes care of flow control by ensuring that
both ends have enough resources and
both can handle the speed of data transfer of each other so that none of them
gets overloaded with data. The term congestion control is used in almost the
same context except that resources and speed of each router is also taken care
of. The main concern is network resources in the
latter case.
·
Multiplexing
/ Demultiplexing: Many applications can be sending/receiving data at
the same time. Data from all of them
has to be multiplexed together. On receiving some data from lower layer, TCP
has to decide which application is the recipient. This is called
demultiplexing. TCP uses the concept of port number to do this.
TCP segment header:
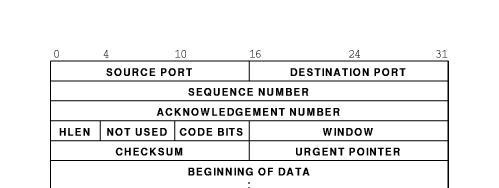
Explanation of header fields:
·
Source
and destination port: These fields identify the local endpoint of the
connection. Each host may decide for
itself how to allocate its own ports starting at 1024. The source
and destination socket numbers together identify
the connection.
·
Sequence
and ACK number: This field is used to give a sequence number to
each and
every
byte transferred. This has an advantage over giving the sequence numbers to
every packet because data of many small packets can be combined into one at the
time of
retransmission, if needed. The ACK signifies the next byte expected from the
source and not the last byte received. The ACKs are cumulative instead of
selective. Sequence number space is as large as 32-bit although 17 bits would
have been enough if the packets were delivered in order. If packets reach in
order, then according to the following formula:
(sender's
window size) + (receiver's window size) < (sequence number space)
the
sequence number space should be 17-bits. But packets may take different routes
and reach out of order. So, we need a larger sequence number space. And for
optimisation, this is 32-bits.
·
Header
length :This field tells how many 32-bit words are contained in the TCP header.
This is needed because the options field is of
variable length.
· Flags : There are six one-bit flags.
1. URG : This bit indicates whether the
urgent pointer field in this packet is being used.
2. ACK :This bit is set to indicate the
ACK number field in this packet is valid.
3. PSH : This bit indicates PUSHed data.
The receiver is requested to deliver the data to the application upon arrival and not buffer it until a full buffer
has been received.
4. RST : This flag is used to reset a
connection that has become confused due to a host crash or some other reason. It is also used to reject an invalid
segment or refuse an attempt to open a connection. This causes an abrupt end to
the connection, if it existed.
5. SYN : This bit is used to establish
connections. The connection request(1st packet in 3-way handshake) has SYN=1 and ACK=0. The connection reply (2nd
packet in 3-way handshake) has SYN=1 and ACK=1.
6. FIN : This bit is used to release a
connection. It specifies that the sender has no more fresh data to transmit. However, it will retransmit any lost or
delayed packet. Also, it will continue to receive data from other side. Since
SYN and FIN packets have to be acknowledged, they must have a sequence number
even if they do not contain any data.
·
Window
Size: Flow control in TCP is handled using a variable-size sliding window. The Window Size field tells how many bytes
may be sent starting at the byte acknowledged. Sender can send the bytes with
sequence number between (ACK#) to (ACK# + window size - 1) A window size of
zero is legal and says that the bytes up to and including ACK# -1 have been
received, but the receiver would like no more data for the moment.
Permission
to send can be granted later by sending a segment with the same ACK
number and a nonzero Window Size field.
·
Checksum
: This is
provided for extreme reliability. It checksums the header, the data, and the conceptual pseudoheader. The
pseudoheader contains the 32-bit IP address of the source and destination
machines, the protocol number for TCP(6), and the byte count for the TCP
segment (including the header).Including the pseudoheader in TCP checksum
computation helps detect misdelivered packets, but doing so violates the
protocol hierarchy since the IP addresses in it belong to the IP layer, not the
TCP layer.
·
Urgent
Pointer: Indicates a byte offset from the current sequence number at which urgent data are to be found. Urgent
data continues till the end of the segment. This is not used in practice. The
same effect can be had by using two TCP connections, one for
transferring urgent data.
·
Options :
Provides
a way to add extra facilities not covered by the regular header. eg, o Maximum
TCP payload that sender is willing to handle. The maximum size of segment is
called MSS (Maximum Segment Size). At the time of handshake, both parties
inform each other about their capacity. Minimum of the two is honoured. This
information is sent in the options of the SYN packets of the three way
handshake. Window scale option can be used to increase the window size. It can
be specified by telling the receiver that the window size should be interpreted
by shifting it left by specified number of bits. This header option allows window
size up to 230.
·
Data: This can
be of variable size. TCP knows its size by looking at the IP size header.
Related Topics