Chapter: Cryptography and Network Security Principles and Practice : Overview
The OSI Security Architecture
THE OSI SECURITY ARCHITECTURE
To assess effectively the security needs of an organization and
to evaluate and choose various security products and policies, the manager
responsible for security needs some systematic way of defining the requirements
for security and characterizing the approaches to satisfying those
requirements. This is difficult enough in a centralized data processing
environment; with the use of local and wide area networks, the problems are
compounded.
ITU-T3 Recommendation X.800, Security
Architecture for OSI, defines such a systematic approach.4 The OSI security architecture is useful to managers as a way of
organizing the task of providing security. Furthermore, because this
architecture was developed as an international standard, computer and
communications vendors have developed security features for their products and
services that relate to this structured definition of services and mechanisms.
For our purposes, the OSI security architecture provides a
useful, if abstract, overview of many of the concepts that this book deals
with. The OSI security archi-tecture focuses on security attacks, mechanisms,
and services. These can be defined briefly as
•
Security
attack: Any
action that compromises the security of information owned by an
organization.
•
Security
mechanism: A process
(or a device incorporating such a process) that is designed to detect,
prevent, or recover from a security attack.
•
Security
service: A
processing or communication service that enhances the security of the
data processing systems and the information transfers of an organization. The
services are intended to counter security attacks, and they make use of one or
more security mechanisms to provide the service.
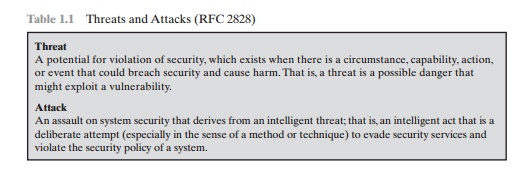
In the literature, the terms threat and attack are
commonly used to mean more or less the same thing. Table 1.1 provides
definitions taken from RFC 2828, Internet Security Glossary.
Related Topics