Chapter: Cryptography and Network Security Principles and Practice : Network and Internet Security : Transport-Level Security
Secure Socket Layer and Transport Layer Security
SECURE SOCKET LAYER AND TRANSPORT
LAYER SECURITY
Netscape originated SSL. Version
3 of the protocol was designed with public review and
input from industry and was published
as an Internet draft document. Subsequently, when a consensus was
reached to submit the protocol for Internet standardization, the TLS working
group was formed
within IETF to develop a common standard. This first published version of TLS can be viewed as essentially
an SSLv3.1 and is very close
to and backward compatible with SSLv3.
This section is devoted
to a discussion of SSLv3.
In the next
section, the principal differences between
SSLv3 and TLS are described.
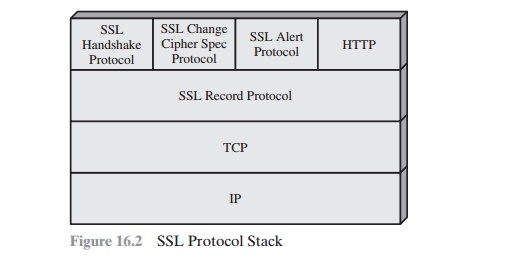
SSL Architecture
SSL is designed
to make use of TCP to provide
a reliable end-to-end secure service. SSL is not
a single protocol but rather
two layers of protocols, as illustrated in Figure 16.2.
The SSL Record Protocol provides basic security services to
various higher- layer protocols. In particular, the Hypertext Transfer Protocol (HTTP), which pro- vides
the transfer service for Web client/server
interaction, can operate on top of SSL. Three
higher-layer protocols are defined as part of SSL: the Handshake
Protocol, The Change Cipher
Spec Protocol, and the Alert
Protocol. These SSL-spe- cific protocols are used in the
management of SSL exchanges and are examined later in this section.
Two important SSL concepts are the SSL
session and the SSL connection, which are defined in the specification as
follows.
•
Connection: A connection is a
transport (in the OSI layering model defini- tion) that provides a suitable
type of service. For SSL, such
connections are peer-to-peer relationships. The connections are transient. Every connection is associated with one session.
•
Session: An SSL session
is an association between a client and a server. Sessions are created by the Handshake Protocol.
Sessions define a set of cryptographic
security
parameters which can be shared
among multiple connections. Sessions are used to avoid the expensive
negotiation of new security parameters for each connection.
Between any pair of parties
(applications such as HTTP on client and server),
there may be multiple secure connections. In theory, there may also be multiple
simultaneous sessions between
parties, but this feature is not used in practice.
There are a number of states associated with
each session. Once a session is established, there is a current operating state
for both read and write (i.e., receive and send). In addition, during the
Handshake Protocol, pending read and write states are created. Upon successful
conclusion of the Handshake Protocol, the pending states become the current
states.
A session state is defined by the following
parameters.
•
Session identifier: An arbitrary byte sequence chosen
by the server to identify an active or resumable
session state.
•
Peer certificate: An X509.v3
certificate of the peer. This element of the state may be null.
•
Compression method: The algorithm used to compress data prior to encryption.
•
Cipher spec: Specifies the bulk data encryption algorithm (such as null,
AES, etc.) and a hash algorithm (such as MD5 or SHA-1) used for MAC calculation.
It also defines cryptographic attributes such as the hash_size.
•
Master secret: 48-byte secret
shared between the
client and server.
•
Is resumable: A flag indicating whether
the session can be used to initiate
new connections.
A connection state is defined by the
following parameters.
•
Server and client random: Byte sequences
that are chosen by the server and client for each connection.
•
Server write MAC secret: The secret key used in MAC
operations on data sent by the server.
•
Client write MAC secret: The secret key used in MAC
operations on data sent by the client.
•
Server write key: The secret encryption key for data encrypted by the server and decrypted by the client.
•
Client write key: The symmetric
encryption key for data encrypted by the client and decrypted by the server.
•
Initialization vectors: When a block cipher
in CBC mode is used,
an initializa- tion vector (IV) is maintained for each key. This field is first initialized by the SSL Handshake Protocol. Thereafter, the final ciphertext block from each record is preserved for use as the IV with the following record.
Sequence numbers: Each party maintains separate sequence
numbers for transmitted
and received messages
for each connection. When a party sends or receives a change cipher
spec message, the appropriate sequence
number is set to
zero. Sequence numbers
may not exceed 264
– 1.
SSL
Record Protocol
The SSL Record Protocol provides two
services for SSL connections:
•
Confidentiality: The Handshake Protocol defines
a shared secret key that is used for conventional encryption of SSL
payloads.
•
Message Integrity: The Handshake Protocol also defines a shared secret
key that is used to form a message
authentication code (MAC).
Figure 16.3 indicates the overall operation
of the SSL Record Protocol. The Record Protocol
takes an application message to be transmitted, fragments the data into
manageable blocks, optionally compresses the data, applies a MAC, encrypts,
adds a header, and transmits
the resulting unit in a TCP segment.
Received data are decrypted,
verified, decompressed, and reassembled before being delivered to higher-level users.
The first
step is fragmentation. Each upper-layer message is
fragmented into blocks of 214 bytes (16384
bytes) or less. Next, compression
is optionally applied. Compression must be lossless
and may not increase the content length by more than 1024 bytes.1In SSLv3 (as well
as the current version of TLS), no compression
algorithm is specified, so
the default compression algorithm is null.
The next step in processing is to compute
a message authentication code over the compressed data.
For this purpose, a shared secret
key is used. The calculation is defined as
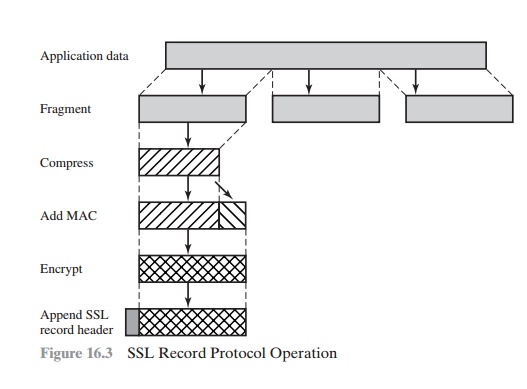
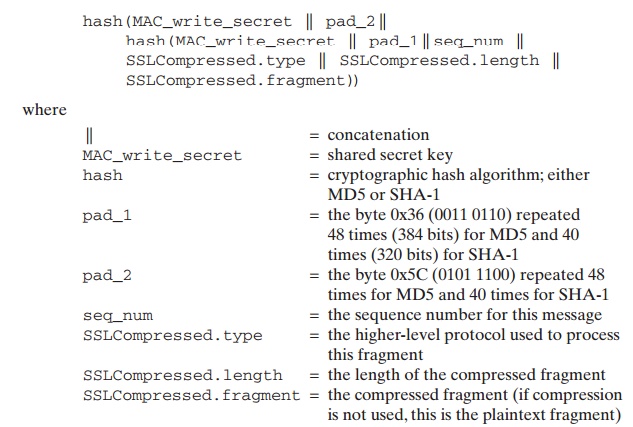
Note that
this is very similar to the HMAC algorithm defined in Chapter
12. The difference is that the two pads are concatenated in SSLv3 and are XORed in HMAC.
The SSLv3 MAC algorithm is based on
the original Internet draft for HMAC, which used concatenation. The final version of HMAC (defined
in RFC 2104) uses the XOR. Next, the compressed message
plus the MAC are encrypted
using symmetric encryption. Encryption may not increase the content length by more than 1024 bytes, so that the total length
may not exceed
214
+ 2048. The following encryption algorithms are permitted:
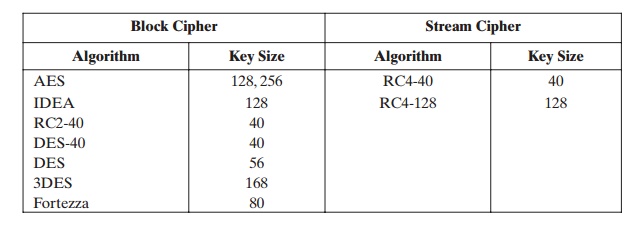
Fortezza can be used in a smart card encryption scheme.
For stream encryption, the compressed message
plus the MAC are encrypted.
Note that the MAC is computed before
encryption takes place and that the MAC is then encrypted along
with the plaintext or compressed plaintext.
For block encryption, padding may be added after the MAC prior to encryp- tion. The padding
is in the form of a number
of padding bytes
followed by a one-byte
indication of the length of the padding.
The total amount of padding is the smallest amount such that the total size of the data to be encrypted (plaintext plus MAC plus padding) is a multiple of the
cipher’s block length. An example is a plaintext (or compressed text if compression is used) of 58 bytes, with a MAC of 20 bytes
(using SHA-1), that is encrypted using a block length of 8 bytes (e.g.,
DES). With the padding-length byte,
this yields a total of 79 bytes. To make the total
an integer multiple of 8, one byte of padding is added.
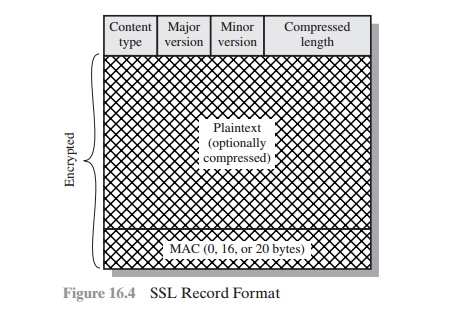
The final step of SSL Record Protocol
processing is to prepare a header consisting of the following fields:
•
Content Type (8 bits): The higher-layer protocol used to process
the enclosed fragment.
•
Major Version (8 bits): Indicates major
version of SSL in use.
For SSLv3, the value is 3.
•
Minor Version (8
bits): Indicates minor version
in use. For SSLv3, the value is 0.
•
Compressed Length (16 bits): The length in bytes of
the plaintext fragment (or compressed fragment if compression is used). The maximum
value is 214 + 2048.
The content
types that have been defined are change_cipher_spec, alert, handshake, and application_data. The first three
are the SSL-specific
protocols, discussed next.
Note that no distinction is made among the various appli- cations (e.g., HTTP) that might use SSL; the content of
the data created by such applications is opaque to SSL.
Figure 16.4 illustrates the SSL record
format.
Change Cipher Spec Protocol
The Change Cipher Spec Protocol
is one of the three SSL-specific protocols
that use the SSL Record
Protocol, and it is the simplest. This protocol consists of a single message (Figure
16.5a), which consists
of a single byte with the value
1. The sole pur- pose of this message
is to cause the pending
state to be copied into the current
state, which updates the cipher suite to be used on this connection.
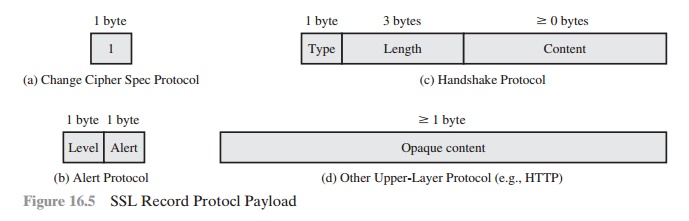
Alert Protocol
The Alert Protocol is used to convey
SSL-related alerts to the peer entity. As with other applications that use SSL,
alert messages are compressed and encrypted, as specified by the current state.
Each message in this protocol consists of
two bytes (Figure 16.5b). The first
byte takes the value warning (1) or fatal (2) to convey the severity of the
message. If the level is fatal, SSL immediately terminates the connection.
Other connections on the same session may
continue, but no new connections on this session may be established. The second
byte contains a code that indicates the specific alert. First, we list those alerts that are always fatal
(definitions from the SSL specification):
•
unexpected_message: An
inappropriate message was received.
•
bad_record_mac: An
incorrect MAC was received.
•
decompression_failure: The decompression function
received improper input (e.g., unable to decompress or decompress to greater
than maximum allowable length).
•
handshake_failure: Sender was unable to negotiate an acceptable set of
security parameters given
the options available.
•
illegal_parameter: A field
in a handshake message was out of range or inconsistent with other fields.
The remaining alerts are the following.
•
close_notify:
Notifies the recipient that the
sender will not send any
more messages on this connection.
Each party is required to send a close_notify alert before
closing the write
side of a connection.
•
no_certificate: May be sent in response to a certificate request if no
appropriate certificate is available.
•
bad_certificate: A
received certificate was corrupt (e.g., contained a signature that did not verify).
•
unsupported_certificate: The type of the received certificate is not supported.
•
certificate_revoked: A
certificate has been revoked by its signer.
•
certificate_expired: A
certificate has expired.
(e)
certificate_unknown: Some
other unspecified issue arose in processing the certificate, rendering it unacceptable.
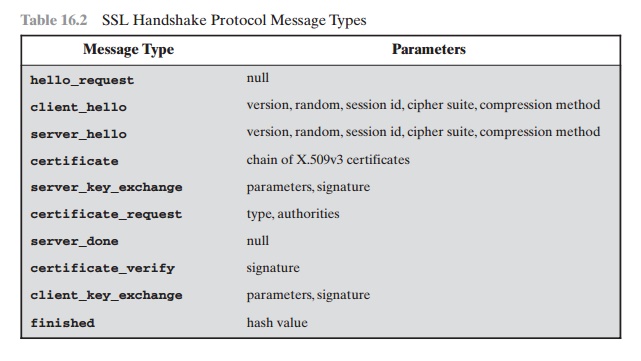
Handshake Protocol
The most complex
part of SSL is the Handshake Protocol. This protocol allows
the server and client to authenticate each other and to negotiate
an encryption and MAC algorithm and
cryptographic keys to be used to protect data sent in an SSL record. The Handshake
Protocol is used before any application data is transmitted.
The Handshake Protocol
consists of a series of messages exchanged
by client and server. All of
these have the format shown in Figure 16.5c. Each message has three fields:
(f)
Type (1 byte): Indicates one of 10 messages. Table 16.2 lists the defined message types.
(g)
Length (3 bytes): The length of the message in bytes.
(h)
Content ( Ú 0 bytes): The parameters associated with this message; these are
listed in Table 16.2.
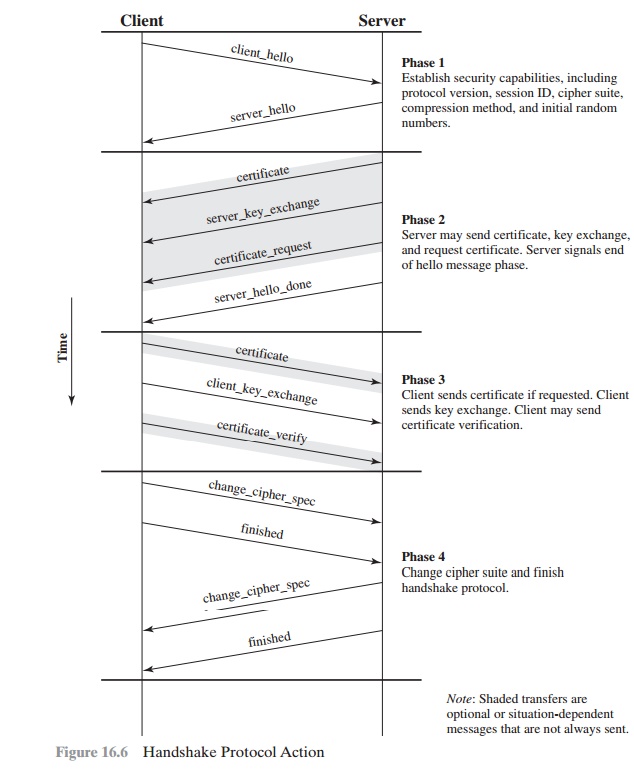
Figure 16.6 shows
the initial exchange
needed to establish a logical connection between client and server.
The exchange can be viewed as having four phases.
PHASE 1. ESTABLISH SECURITY CAPABILITIES This phase is used to initiate a logical
connection and to establish the security capabilities that will be associated
with it. The exchange is initiated by the client,
which sends a client_hello message with the following parameters:
(i)
Version: The highest SSL version understood by the client.
(j)
Random: A client-generated random
structure consisting of a 32-bit
timestamp and 28 bytes generated by a secure random number generator.
These values serve as nonces
and are used during key exchange to prevent replay
attacks.
Table 16.2
SSL Handshake Protocol
Message Types
•
Session ID: A variable-length
session identifier. A nonzero value indicates that the client wishes
to update the parameters of an existing
connection or to create a new connection on this session.
A zero value indicates that the client wishes to establish a new connection on a new session.
•
CipherSuite: This is a list that
contains the combinations of cryptographic algorithms supported by the client,
in decreasing order of preference. Each element of the list (each cipher suite)
defines both a key exchange algorithm and a CipherSpec; these are discussed subsequently.
•
Compression
Method: This is a list of the compression methods the client supports.
After sending the client_hello message, the client waits for the
server_hello message, which contains the same parameters as
the client_hello message. For the server_hello message, the following
conven- tions apply. The Version field contains the
lower of the versions suggested by the client and the highest supported by the
server. The Random field is
generated by the server and is independent of the client’s
Random field. If the SessionID field of the client was nonzero,
the same value is used by the server; otherwise
the server’s SessionID field contains the value for a new session. The CipherSuite field contains the single
cipher suite selected
by the server from those
proposed by the client. The Compression
field contains the compression method selected by the server from those
proposed by the client.
The first element of the CipherSuite
parameter is the key exchange method (i.e., the means by which the
cryptographic keys for conventional encryption and MAC are exchanged). The
following key exchange methods are supported.
•
RSA: The secret key is encrypted with
the receiver’s RSA public
key. A public- key certificate for the receiver’s key
must be made
available.
•
Fixed Diffie-Hellman: This is a Diffie-Hellman
key exchange in which the server’s
certificate contains the Diffie-Hellman public parameters signed by the
certificate authority (CA). That is, the
public-key certificate contains the Diffie-Hellman public-key parameters. The client provides its Diffie-Hellman
public-key parameters either in a certificate, if client authentication is required, or in a key exchange
message. This method results in a fixed secret
key between two peers based on the Diffie-Hellman calculation using the
fixed public keys.
•
Ephemeral Diffie-Hellman: This
technique is used to create ephemeral (temporary, one-time) secret keys. In this case, the Diffie-Hellman public keys
are exchanged, signed using the sender’s private RSA or DSS key. The receiver can use the corresponding public key to verify
the signature. Certificates are used to authenticate the public keys.
This would appear to be the most secure
of the three Diffie-Hellman options,
because it results
in a temporary, authenticated key.
•
Anonymous Diffie-Hellman: The base Diffie-Hellman algorithm is used with
no authentication. That is, each
side sends its
public Diffie-Hellman parameters to the other with no authentication. This approach
is vulnerable to man-in-the-
middle attacks, in which
the attacker conducts anonymous Diffie-Hellman with both parties.
•
Fortezza: The technique defined
for the Fortezza scheme.
Following the definition of a key exchange
method is the CipherSpec, which
includes the following fields.
CipherAlgorithm: Any of the algorithms mentioned earlier: RC4,
RC2, DES, 3DES, DES40, IDEA, or Fortezza
•
MACAlgorithm:
MD5 or SHA-1
•
CipherType: Stream or Block
•
IsExportable: True or False
•
HashSize: 0, 16 (for MD5), or 20 (for SHA-1) bytes
•
Key Material: A
sequence of bytes that contain data used in generating the write keys
•
IV Size: The size of the Initialization Value for Cipher Block
Chaining (CBC) encryption
PHASE 2. SERVER AUTHENTICATION AND KEY EXCHANGE The server begins
this phase by sending
its certificate if it needs
to be authenticated; the message
contains one or a chain of X.509 certificates. The certificate message
is required for any agreed-on
key exchange method except anonymous
Diffie-Hellman. Note that if fixed Diffie-
Hellman is used, this certificate message functions as the server’s key exchange message because it contains the
server’s public Diffie-Hellman parameters.
Next, a server_key_exchange message may be sent if it is required.
It is not required in two instances:
(1) The server has sent a certificate
with fixed Diffie-Hellman parameters or (2) a RSA
key exchange is to be used. The server_key_exchange message is needed for the following:
•
Anonymous Diffie-Hellman: The message content
consists of the two global Diffie-Hellman values (a prime
number and a primitive root of that number) plus the server’s public
Diffie-Hellman key (see Figure 10.1).
•
Ephemeral Diffie-Hellman: The message content
includes the three Diffie- Hellman parameters provided for anonymous
Diffie-Hellman plus a signature
of those parameters.
•
RSA key exchange (in which the server is using RSA but has a signature-only RSA
key): Accordingly,
the client cannot simply send a secret key encrypted with the server’s public key. Instead, the server must create a
temporary RSA public/private key pair and use the server_key_exchange message to send
the public
key. The message content includes the two parameters
of the temporary RSA public key (exponent and modulus; see Figure 9.5) plus a
signature of those parameters.
•
Fortezza
Some further details
about the signatures are warranted. As usual, a signature
is created by taking the hash of a message
and encrypting it with the sender’s private key. In this case,
the hash is defined as
hash(ClientHello.random | ServerHello.random | ServerParams)
So the hash covers not only the Diffie-Hellman or RSA parameters but also the two
nonces from the initial hello messages. This ensures against replay attacks and
misrepresentation. In the case of a DSS signature, the hash is performed
using the SHA-1 algorithm. In the case
of an RSA signature, both an MD5 and an SHA-1 hash are calculated, and the concatenation of the two hashes (36 bytes) is encrypted
with the server’s private key.
Next, a nonanonymous server (server not
using anonymous Diffie-Hellman) can request a certificate from the client.
The certificate_request message includes
two parameters: certificate_type and certificate_authorities.
The certificate type indicates the public-key algorithm and its use:
•
RSA, signature only
•
DSS, signature only
•
RSA
for fixed
Diffie-Hellman; in this case the signature is used only for authentication, by sending a certificate signed
with RSA
•
DSS for fixed Diffie-Hellman; again, used only for authentication
•
RSA for ephemeral Diffie-Hellman
•
DSS for ephemeral Diffie-Hellman
•
Fortezza
The second parameter in the certificate_request message is a list of the distinguished names of acceptable certificate authorities.
The final message in phase 2, and one that
is always required, is the server_done
message, which is sent by the
server to indicate the end of the server hello and associated messages. After
sending this message, the server will wait for a client response. This message
has no parameters.
PHASE 3. CLIENT AUTHENTICATION
AND KEY EXCHANGE Upon receipt of
the
server_done message,
the client should verify that the server provided a valid certificate (if required)
and check that the server_hello parameters are acceptable.
If all is satisfactory, the client
sends one or more messages back to the server.
If the server
has requested a certificate, the client begins
this phase by sending
a certificate
message. If no suitable
certificate is available, the client sends a no_certificate alert instead.
Next is the client_key_exchange message, which must be sent in this phase. The content of the
message depends on the type of key exchange, as follows.
•
RSA: The client generates a 48-byte pre-master
secret and encrypts with the public key from the server’s
certificate or temporary RSA key from
a server_key_exchange message. Its
use to compute a master secret is explained later.
•
Ephemeral or Anonymous Diffie-Hellman: The client’s public
Diffie-Hellman parameters are sent.
•
Fixed Diffie-Hellman: The client’s public
Diffie-Hellman parameters were sent in a certificate message,
so the content of this message is null.
•
Fortezza: The client’s Fortezza parameters are sent.
Finally, in this phase, the client may send a certificate_verify message to
provide explicit verification of a client certificate. This message is only
sent fol- lowing any client certificate that has signing capability (i.e., all
certificates except those containing fixed Diffie-Hellman parameters). This message signs a hash code
based on the preceding messages,
defined as
CertificateVerify.signature.md5_hash=
MD5(master_secret | pad_2 | MD5(handshake_messages | master_secret | pad_1));
CertificateVerify.signature.sha_hash=
SHA(master_secret | pad_2 | SHA(handshake_messages | master_secret | pad_1));
where pad_1 and
pad_2 are the values defined earlier for the MAC, handshake_messages refers to all Handshake Protocol messages sent or received starting at client_hello but not including
this message, and master_secret is the calculated secret
whose construction is explained later
in this section. If the user’s private key is DSS, then it is used to encrypt the SHA-1 hash. If the user’s
private key is RSA, it is used to encrypt
the concatenation of the
MD5 and SHA-1 hashes. In either case,
the purpose is to verify
the client’s owner- ship of the private key for the
client certificate. Even if someone is misusing the client’s certificate, he or she would be unable to send this message.
PHASE 4. FINISH This phase completes the setting up of a secure
connection. The client sends
a change_cipher_spec message and copies the pending CipherSpec into the current CipherSpec. Note that this message is not considered
part of the Handshake Protocol but is sent using the Change Cipher Spec
Protocol. The client then immediately sends
the finished message under the new algorithms, keys, and secrets. The finished message verifies
that the key exchange and authentication processes were successful. The content
of the finished message is the concatenation of two hash values:
MD5(master_secret | pad2 | MD5(handshake_messages | Sender | master_secret | pad1))
SHA(master_secret | pad2 | SHA(handshake_messages | Sender | master_secret | pad1))
where Sender is a code that
identifies that the sender is the
client and handshake_messages is all of the data from all handshake
messages up to but
not including this message.
In response
to these two messages, the server sends its own change_cipher_spec message, transfers the pending to the current
CipherSpec, and sends its finished message. At this point, the handshake
is complete and the client and server may begin to exchange application-layer data.
Cryptographic Computations
Two further items are of interest: (1) the creation
of a shared master secret by means of the key exchange and (2) the
generation of cryptographic parameters from the master secret.
MASTER SECRET
CREATION The
shared master secret is a one-time 48-byte value (384 bits) generated for this session by
means of secure key exchange. The creation is in two stages.
First, a pre_master_secret
is exchanged.
Second, the master_secret
is calculated
by both parties. For pre_master_secret exchange, there are two
possibilities.
•
RSA: A 48-byte
pre_master_secret is generated by the
client, encrypted with the
server’s public RSA key, and sent to
the server. The server decrypts the ciphertext using its private
key to recover the pre_master_secret.
•
Diffie-Hellman: Both client and server generate
a Diffie-Hellman public
key. After these
are exchanged, each side performs
the Diffie-Hellman calculation to create the shared pre_master_secret.
Both sides now compute the master_secret as
master_secret
= MD5(pre_master_secret | SHA('A' |
pre_master_secret | ClientHello.random | ServerHello.random)) ||
MD5(pre_master_secret | SHA('BB' | pre_master_secret | ClientHello.random | ServerHello.random)) |
MD5(pre_master_secret | SHA('CCC' | pre_master_secret | ClientHello.random | ServerHello.random))
where ClientHello.random and ServerHello.random are the two nonce values
exchanged in the initial hello messages.
GENERATION OF CRYPTOGRAPHIC PARAMETERS
CipherSpecs require a client write MAC
secret, a server write MAC secret, a client write key, a server write key, a client write IV, and a server write IV, which are generated from the master
secret in that order. These parameters are generated from the master
secret by hashing
the master secret into a sequence
of secure bytes of sufficient length for all needed parameters.
The generation of the key material from the master secret uses the same format
for generation of the master secret from the pre-master secret as
key_block = MD5(master_secret | SHA('A' | master_secret | ServerHello.random | ClientHello.random)) ||
MD5(master_secret | SHA('BB' | master_secret | ServerHello.random | ClientHello.random)) ||
MD5(master_secret | SHA('CCC' | master_secret | ServerHello.random | ClientHello.random)) ||...
until enough output
has been generated. The result
of this algorithmic structure is a pseudorandom function. We can view the master_secret as the pseudorandom seed value to the function. The client
and server random
numbers can be viewed as salt
values to complicate cryptanalysis (see Chapter
20 for a discussion of the use of
salt values).
Related Topics