Chapter: Information Security : Security Investigation
Risk Control Strategies
RISK CONTROL STRATEGIES
Four
basic strategies to control each of the risks that result from these
vulnerabilities.
ü Apply
safeguards that eliminate the remaining uncontrolled risks for the
vulnerability [Avoidance]
ü Transfer
the risk to other areas (or) to outside entities[transference]
ü Reduce
the impact should the vulnerability be exploited[Mitigation]
ü Understand
the consequences and accept the risk without control or mitigation[Acceptance]
1 Avoidance
It is the
risk control strategy that attempts to prevent the exploitation of the
vulnerability, and is accomplished by means of
Countering threats
Removing Vulnerabilities in assets
Limiting access to assets
Adding protective safeguards.
Three
common methods of risk avoidance are
Application of policy
Application of Training & Education
Application of Technology
2 Transference
Transference
is the control approach that attempts to shift the risk to other assets, other
processes, or other organizations.
It may be
accomplished through rethinking how services are offered, revising deployment
models, outsourcing to other organizations, purchasing Insurance, Implementing
Service contracts with providers.
Top 10
Information Security mistakes made by individuals.
Passwords on Post-it-Notes
Leaving unattended computers on.
Opening e-mail attachments from strangers.
Poor Password etiquette
Laptops on the loose (unsecured laptops that are
easily stolen)
Blabber mouths ( People who talk about passwords)
Plug & Play[Technology that enables hardware
devices to be installed and configured without the protection provided by
people who perform installations]
Unreported Security Violations
Always behind the times.
Not watching for dangers inside the organization
3 Mitigation
It is the control approach that attempts to reduce the impact caused by
the exploitation of vulnerability through planning & preparation.
ü Mitigation
begins with the early detection that an attack is in progress and the ability
of the organization to respond quickly, efficiently and effectively.
ü Includes
3 types of plans.
1. Incident
response plan (IRP) -Actions to take while incident is in progress
2. Disaster
recovery plan (DRP) - Most common mitigation procedure.
3. Business
continuity plan (BCP) - Continuation of business activities if catastrophic
event occurs.
1.Incident Response Plan (IRP)
This IRP
Plan provides answers to questions such as
What do I do now?
What should the administrator do first?
Whom should they contact?
What should they document?
2.The IRP Supplies answers.
ü For
example, a system’s administrator may notice that someone is copying
information from the server without authorization, signaling violation of
policy by a potential hacker or an unauthorized employee.
ü The IRP also enables the organization to
take coordinated action that is either predefined and specific or ad hoc and reactive.
3.Disaster Recovery Plan (DRP)
ü Can
include strategies to limit losses before and during the disaster.
ü Include
all preparations for the recovery process, strategies to limit losses during
the disaster, and detailed steps to follow when the smoke clears, the dust
settles, or the floodwater recede.
ü DRP
focuses more on preparations completed before and actions taken after the
incident, whereas the IRP focuses on intelligence gathering, information
analysis, coordinated decision making, and urgent, concrete actions.
4.Business Continuity Plan (BCP)
2. BCP is
the most strategic and long term of the three plans.
It encompasses the continuation of business activities if a catastrophic
event occurs, such as the loss of an entire database, building or operations
center.
- The BCP
includes planning the steps necessary to ensure the continuation of the
organization when the scope or scale of a disaster exceeds the ability of the
DRP to restore operations.
- Many
companies offer this service as a contingency against disastrous events such as
fires. Floods, earthquakes, and most natural disasters.
4 Acceptance
- It is the
choice to do nothing to protect a vulnerability and do accept the outcome of
its exploitation.
- This
strategy occurs when the organization has:
Determined the level of risk.
Assessed the probability of attack.
Estimated the potential damage that could occur
from attacks.
Performed a thorough cost benefit analysis.
Evaluated controls using each appropriate type of
feasibility.
Decided that the particular function, service,
information, or asset did not justify the cost of protection.
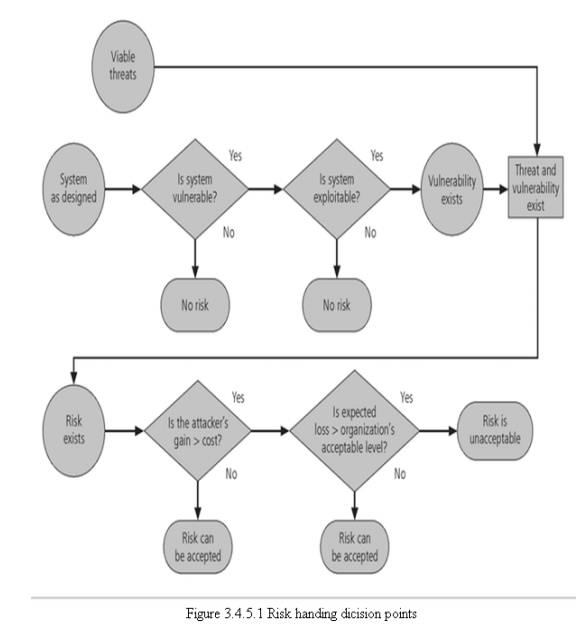
5 Selecting a Risk Control Strategy
- Level of
threat and value of asset play major role in selection of strategy
- Rules of
thumb on strategy selection can be applied:
When vulnerability (flaw or weakness) exists:
Implement security controls to reduce the likelihood of a vulnerability being
exercised.
When vulnerability can be exploited: Apply layered
protections, architectural designs, and administrative controls to minimize the
risk.
When the attacker’s cost is less than his potential
gain: Apply protections to increase the attacker’s cost.
When potential loss is substantial: Apply design
principles, architectural designs, and technical and non-technical protections
to limit the extent of the attack, thereby reducing the potential for loss.
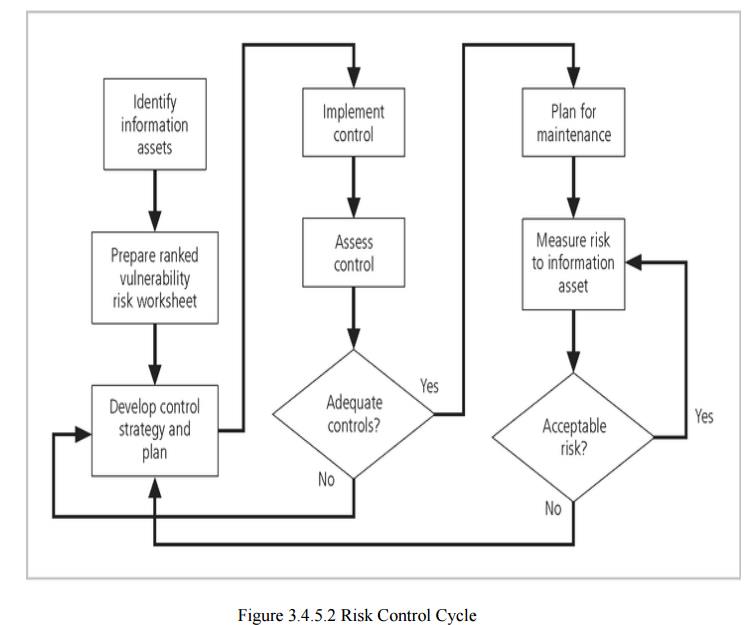
6 Evaluation, Assessment & Maintenance of Risk
Controls
Once a
control strategy has been implemented, it should be monitored, & measured
on an ongoing basis to determine the effectiveness of the security controls and
the accuracy of the estimate of the Residual risk
There is
no exit from this cycle; it is a process that continues for as long as the
organization continues to function.
Categories of Controls
ü Controlling
risk through avoidance, Mitigation or Transference may be accomplished by
implementing controls or safeguards.
ü Four ways
to categorize controls have been identified.
–
Control function
Preventive or detective
–
Architectural layer
One or more layers of technical architecture
–
Strategy layer
Avoidance, mitigation …
–
Information security principle
Control Function
· Safeguards
designed to defend systems are either preventive or detective.
· Preventive
controls stop attempts to exploit a vulnerability by implementing a security
principle, such as authentication, or Confidentiality.
· Preventive
controls use a technical procedure, such as encryption, or some combination of
technical means and enforcement methods.
· Detective
controls – warn organizations of violations of security principles,
organizational policies, or attempts to exploit vulnerabilities.
· Detective
controls use techniques such as audit trails, intrusion detection and
configuration monitoring.
Architectural Layer
ü Controls
apply to one or more layers of an organization’s technical architecture.
ü The
following entities are commonly regarded as distinct layers in an
organization’s
Information
architecture.
Organizational policy.
External Networks.
Extranets ( or demilitarized zones )
Intranets ( WANs and LANs )
ü Network
devices that interface network zones.(Switches, Routers, firewalls and hubs)
ü Systems [
Mainframe, Server, desktop]
ü Applications.
Strategy Layer
1. Controls
are sometimes classified by the risk control strategy they operate within:
Avoidance
Mitigation
transference
Characteristics of Secure Information
ü Confidentiality
ü Integrity
ü Availability
ü Authentication
ü Authorization
ü Accountability
ü Privacy
Confidentiality: The control assures the
confidentiality of data when it is stored, processed, or transmitted. An example of this type of control is the use of
Secure Sockets Layer (SSL) encryption technology to secure Web content as it
moves from Web server to browser.
Integrity: The control assures that the
information asset properly, completely, and correctly receives, processes, stores, and retrieves data in a consistent
and correct manner .Ex: Use of parity or cyclical redundancy checks in data
transmission protocols.
Availability: The control assures ongoing
access to critical information assets. Ex: Deployment of a network operations center using a sophisticated network
monitoring toolset.
Authentication: The control assures that the
entity (person or computer) accessing information assets is in fact the stated entity. Ex: The use of cryptographic
certificates to establish SSL connections, or the use of cryptographic hardware
tokens such as SecurID cards as a second authentication of identity.
Authorization: The control assures that a user
has been specifically and explicitly authorized to access, update, or delete the contents of an information asset.
Ex: Use of access control lists and authorization groups in the Windows
networking environment. Another example is the use of a database authorization scheme
to verify the designated users for each function.
Accountability: The control assures that every
activity undertaken can be attributed to a specific named person or automated process. Ex: Use of audit logs to track
when each user logged in and logged out of each computer.
Privacy:
The control assures that the procedures to access, update, or remove personally
identifiable information comply with the applicable laws and policies for that
kind of information.
7 Feasibility Studies
Before
deciding on the strategy (Avoidance, transference, mitigation, or acceptance),
for a specific vulnerability, all the economic and non-economic consequences of
the vulnerability facing the information asset must be explored.
Cost Avoidance- It is the process of avoiding
the financial impact of an incident by implementing
a control.
Includes
Cost Benefit analysis
Organizational feasibility
Operational Feasibility
Technical Feasibility
Political feasibility.
Cost Benefit Analysis (CBA)
ü Organizations
are urged to begin the cost benefit analysis by evaluating the worth of the
information assets to be protected and the loss in value if those information
assets were compromised by the exploitation of a specific vulnerability.
ü The
formal process to document this decision making process is called a Cost
Benefit analysis or an economic feasibility study.
Cost Benefit Analysis or an
Economic Feasibility study
ü Some of
the items that affect the cost of a control or safeguard include:
Cost of development or acquisition [purchase cost]
of hardware, software and services.
Training Fees(cost to train personnel)
Cost of Implementation[Cost to install, Configure,
and test hardware, software and services]
service Costs[Vendor fees for maintenance and
upgrades]
Cost of maintenance[Labor expense to verify and
continually test, maintain and update]
ü Benefit
is the value that an organization realizes by using controls to prevent losses
associated with a specific vulnerability.
Amount of benefit = Value of the
Information asset and Value at risk.
ü Asset
Valuation is the process of assigning financial value or worth to each
information asset.
ü Some of
the components of asset valuation include:
1. Value
retained from the cost of creating the
information asset.
ü Value
retained from past maintenance of the information asset.
ü Value
implied by the cost of replacing the information.
ü Value
from providing the information.
ü Value
incurred from the cost of protecting the information.
ü Value to
owners.
ü Value of
intellectual property.
ü Value to
adversaries.
ü Loss of
Productivity while the information assets are unavoidable.
ü Loss of
revenue while information assets are unavailable.
ü The
organization must be able to place a dollar value on each collection of
information and the information assets it owns. This value is based on the
answers to these questions:
How much
did it cost to create or acquire this information?
How much
would it cost to recreate or recover this information?
How much
does it cost to maintain this information?
How much
is this information worth to the organization?
How much
is this information worth to the competition?
ü A Single loss expectancy (SLE) is the
calculation of the value associated with the most likely loss from an attack. It is a calculation based on the value
of the asset and the exposure factor
(EF), which is the expected percentage of loss that would occur from a particular attack, as follows:
Single Loss Expectancy (SLE) = Asset value x
Exposure factor [EF]
ü EF à Expected percentage of loss that would occur from a particular attack.
ü The
probability of threat occurring is usually a loosely derived table indicating
the probability of an attack from each threat type within a given time frame
(for example, once every 10 years). This value is commonly referred to as the annualized rate of occurrence (ARO)
ü The
expected value of a loss can be stated in the following equation:
ü Annualized loss Expectancy (ALE) which is
calculated from the ARO and SLE.
ALE = SLE x ARO
Cost Benefit Analysis (CBA)Formula
ü CBA is
whether or not the control alternative being evaluated is worth the associated
cost incurred to control the specific vulnerability.
ü The CBA
is most easily calculated using the ALE from earlier assessments before the
implementation of the proposed control, which is known as ALE (prior).
ü Subtract
the revised ALE, estimated based on control being in place, known as ALE
(post). Complete the calculation by subtracting the annualized cost of the
safeguard (ACS).
CBA = ALE (Prior) - ALE (Post) – ACS
Where:
ALE prior
is the Annualized Loss Expectancy of the risk before the implementation of the
control.
ALE post
is the ALE examined after the control has been in place for a period of time.
ACS is
the Annual Cost of the Safeguard.
8 Bench Marking
An
alternative approach to risk management
Process
of seeking out and studying the practices used in other organizations that
produce results you would like to duplicate in your organization.
One of
two measures typically used to compare practices:
– Metrics-based
measures
– Process-based
measures
Good for
potential legal protection.
Metrics-based measures are
comparisons based on numerical standards, such as:
Numbers of successful attacks.
Staff-hours spent on systems protection.
Dollars spent on protection.
Numbers of Security Personnel.
Estimated value in dollars of the information lost
in successful attacks.
Loss in productivity hours associated with
successful attacks.
The
difference between an organization’s measures and those of others is often
referred to as a performance gap. The other measures commonly used in
benchmarking are process-based measures. Process-based
measures are generally less focused on numbers and more strategic than
metrics-based-measures.
Due Care/Due Diligence
- When
organizations adopt levels of security for a legal defense, they may need to
show that they have done what any prudent organization would do in similar
circumstances - this is referred to as a standard of due care
- Due
diligence is the demonstration that the organization is diligent in ensuring
that the implemented standards continue to provide the required level of
protection
- Failure
to support a standard of due care or due diligence can open an organization to
legal liability
Best Business Practices
ü Security
efforts that provide a superior level of protection of information are referred
to as best business practices
ü Best
security practices (BSPs) are security efforts that are among the best in the
industry
ü When
considering best practices for adoption in your organization, consider the
following:
– Does your organization resemble the
identified target?
– Are the resources you can expend similar?
– Are you in a similar threat environment?
Microsoft’s Ten Immutable Laws of Security
ü If a bad
guy can persuade you to run his program on your computer, it’s not your
computer anymore
ü If a bad
guy can alter the operating system on your computer, it’s not your computer
anymore
ü If a bad
guy has unrestricted physical access to your computer, it’s not your computer
anymore
ü If you
allow a bad guy to upload programs to your web site, it’s not your web site
anymore
ü Weak
passwords trump strong security
ü A machine
is only as secure as the administrator is trustworthy
ü Encrypted
data is only as secure as the decryption key
ü An out of
date virus scanner is only marginally better than no virus scanner at all
ü Absolute
anonymity isn't practical, in real life or on the web
10.
Technology is not a panacea
Problems
ü The
biggest problem with benchmarking in information security is that organizations
don’t talk to each other.
ü Another
problem with benchmarking is that no two organizations are identical
ü A third
problem is that best practices are a moving target.
ü One last
issue to consider is that simply knowing what was going on a few years ago, as
in benchmarking, doesn’t necessarily tell us what.
Baselining
ü Baselining
is the analysis of measures against established standards,
ü In
information security, baselining is comparing security activities and events
against the organization’s future performance.
ü When
baselining it is useful to have a guide to the overall process
Feasibility Studies and the Cost Benefit analysis
ü Before
deciding on the strategy for a specific vulnerability all information about the
economic and non-economic consequences of the vulnerability facing the
information asset must be explored.
ü Fundamentally
we are asking “What are the actual and perceived advantages of implementing a
control contrasted with the actual and perceived disadvantages of implementing
the control?”
Cost Benefit Analysis (CBA)
ü The most
common approach for a project of information Security controls and safeguards
is the economic feasibility of implementation.
ü Begins by
evaluating the worth of information assets are compromised.
ü It is
only common sense that an organization should not spend more to protect an
asset than it is worth.
ü The
formal process to document this is called a cost benefit analysis or an
economic feasibility study.
CBA: Cost Factors
ü Some of
the items that the cost of a control or safeguard include:
ü Cost of
Development or Acquisition
ü Training
Fees
ü Cost of
implementation.
ü Service
Costs
ü Cost of
Maintenance
CBA: Benefits
ü Benefit
is the value that the organization recognizes by using controls to prevent
losses associated with a specific vulnerability.
ü This is
usually determined by valuing the information asset or assets exposed by the
vulnerability and then determining how much of that value is at risk.
CBA: Asset Valuation
ü Asset
Valuation is the process of assigning financial value or worth to each
information asset.
ü The
valuation of assets involves estimation of real and perceived costs associated
with the design, development, installation, maintenance, protection, recovery,
and defense against market loss and litigation.
ü These
estimates are calculated for each set of information bearing systems or
information assets.
ü There are
many components to asset valuation.
CBA: Loss Estimates
· Once the
worth of various assets is estimated examine the potential loss that could
occur from the exploitation of vulnerability or a threat occurrence.
· This
process results in the estimate of potential loss per risk.
· The
questions that must be asked here include:
–
What
damage could occur, and what financial impact would it have?
–
What
would it cost to recover from the attack, in addition to the costs above?
–
What is
the single loss expectancy for each risk?
Organizational Feasibility
ü Organizational
Feasibility examines how well the proposed information security alternatives
will contribute to the efficiency, effectiveness, and overall operation of an
organization.
ü Above and
beyond the impact on the bottom line, the organization must determine how the
proposed alternatives contribute to the business objectives of the
organization.
Operational feasibility
ü Addresses
user acceptance and support, management acceptance and support, and the overall
requirements of the organization’s stake holders.
ü Sometimes
known as behavioral feasibility, because it measures the behavior of users.
ü One of
the fundamental principles of systems development is obtaining user buy in on a
project and one of the most common methods for obtaining user acceptance and
support is through user involvement obtained through three simple steps:
· Communicate
· Educate
· Involve
Technical Feasibility
ü The
project team must also consider the technical feasibilities associated with the
design, implementation, and management of controls.
ü Examines
whether or not the organization has or can acquire the technology necessary to
implement and support the control alternatives.
Political feasibility
ü For some
organizations, the most significant feasibility evaluated may be political
ü Within
Organizations, political feasibility defines what can and cannot occur based on
the consensus and relationships between the communities of interest.
ü The
limits placed on an organization’s actions or a behavior by the information
security controls must fit within the realm of the possible before they can be
effectively implemented, and that realm includes the availability of staff
resources.
Risk Management Discussion Points
ü Not every
organization has the collective will to manage each vulnerability through the
application of controls
– Depending
on the willingness to assume risk, each organization must define its risk appetite
– Risk
appetite defines the quantity and nature of risk that organizations are willing
to accept as they evaluate the
tradeoffs between perfect security and unlimited accessibility
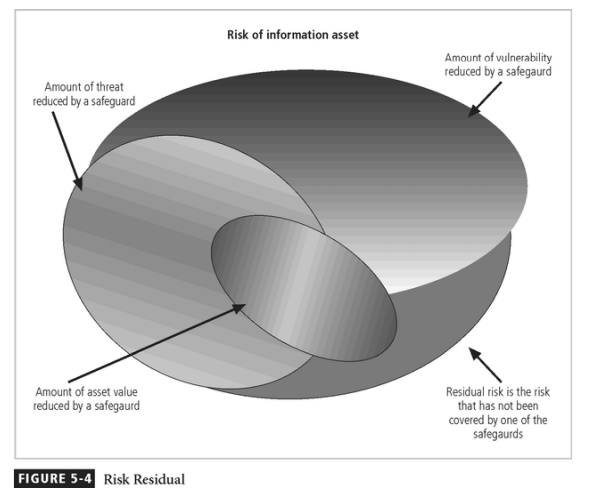
Residual Risk
ü When we
have controlled any given vulnerability as much as we can, there is often risk
that has not been completely removed or has not been completely shifted or
planned for this remainder is called residual risk.
ü To
express it another way, “Residual risk is a combined function of
\endash A threat less the effect of some threat
–reducing safeguards.
\endash Vulnerability less the effect of some
vulnerability- reducing safeguards.
3. an asset
less the effect of some asset value-reducing safeguards “
Documenting Results
ü At
minimum, each infor mation asset-vulnerability pair should have a do cumented
control strategy that clearly iden tifies any residual risk remaining after the
proposed strategy has been executed.
ü Some
organizations doc ument the outcome of the control strategy for each
information asset-vulnerability pair a s an action plan
ü This
action plan includ es concrete tasks, each with accountability assigned to an
organizational unit or to an individual
Recommended Practices in Controlling Risk
We must convince budget authorities to spend up to the value of the
asset to protect a particular asset from an i dentified threat
Each and
every control or safeguard implemented will impact more than one threat-asset
pair
Qualitative Measures
1. The
spectrum of steps described above was performed with real numbers or best guess
estimates of real numbers-this is known as a quantitative assessment.
2. However,
an organization could determine that it couldn’t put specific numbers on these
values.
3. Fortunately,
it is possible to repeat these steps using estimates based on a qualitative
assessment.
4. Instead
of using specific numbers, ranges or levels of values can be developed
simplifying the process
Delphi Technique
1 One
technique for accurately estimating scales and values is the Delphi Technique.
2 The
Delphi Technique, named for the Oracle at Delphi, is a process whereby a group
of individuals rate or rank a set of information
3 The
individual responses are compiled and then returned to the individuals for
another iteration
4 This
process continues until the group is satisfied with the result.
Related Topics