Chapter: Cryptography and Network Security Principles and Practice : Overview
The Challenges of Computer Security
The
Challenges of Computer Security
Computer and network security is both fascinating and complex.
Some of the reasons follow:
1.
Security
is not as simple as it might first appear to the novice. The require-ments seem
to be straightforward; indeed, most of the major requirements for security
services can be given self-explanatory, one-word labels: confi-dentiality,
authentication, nonrepudiation, or integrity. But the mechanisms used to meet
those requirements can be quite complex, and understanding them may involve
rather subtle reasoning.
2.
In
developing a particular security mechanism or algorithm, one must always
consider potential attacks on those security features. In many cases,
successful attacks are designed by looking at the problem in a completely
different way, therefore exploiting an unexpected weakness in the mechanism.
Because of point 2, the procedures used to provide particular
services are often counterintuitive. Typically, a security mechanism is
complex, and it is not obvious from the statement of a particular requirement that
such elaborate measures are needed.
It is only when the various aspects of the threat are considered that elaborate
security mechanisms make sense.
4.
Having
designed various security mechanisms, it is necessary to decide where to use
them. This is true both in terms of physical placement (e.g., at what points in
a network are certain security mechanisms needed) and in a logical sense [e.g.,
at what layer or layers of an architecture such as TCP/IP (Transmission Control
Protocol/Internet Protocol) should mechanisms be placed].
5.
Security
mechanisms typically involve more than a particular algorithm or protocol. They
also require that participants be in possession of some secret information
(e.g., an encryption key), which raises questions about the creation,
distribution, and protection of that secret information. There also may be a
reliance on communications protocols whose behavior may compli-cate the task of
developing the security mechanism. For example, if the proper functioning of
the security mechanism requires setting time limits on the transit time of a
message from sender to receiver, then any protocol or network that introduces
variable, unpredictable delays may render such time limits meaningless.
6.
Computer
and network security is essentially a battle of wits between a perpetrator who
tries to find holes and the designer or administrator who tries to close them.
The great advantage that the attacker has is that he or she need only find a
single weakness, while the designer must find and eliminate all weaknesses to
achieve perfect security.
7.
There
is a natural tendency on the part of users and system managers to perceive
little benefit from security investment until a security failure occurs.
8.
Security
requires regular, even constant, monitoring, and this is difficult in today’s
short-term, overloaded environment.
9.
Security
is still too often an afterthought to be incorporated into a system after the
design is complete rather than being an integral part of the design process.
10.
Many
users and even security administrators view strong security as an imped-iment
to efficient and user-friendly operation of an information system or use of
information.
The difficulties just enumerated will be encountered in numerous
ways as we examine the various security threats and mechanisms throughout this
book.
To assess effectively the security needs of an organization and
to evaluate and choose various security products and policies, the manager
responsible for security needs some systematic way of defining the requirements
for security and characterizing the approaches to satisfying those
requirements. This is difficult enough in a centralized data processing
environment; with the use of local and wide area networks, the problems are
compounded.
ITU-T3 Recommendation X.800, Security
Architecture for OSI, defines such a systematic approach.4 The OSI security architecture is useful to managers as a way of
organizing the task of providing security. Furthermore, because this
architecture was developed as an international standard, computer and
communications vendors have developed security features for their products and
services that relate to this structured definition of services and mechanisms.
For our purposes, the OSI security architecture provides a
useful, if abstract, overview of many of the concepts that this book deals
with. The OSI security archi-tecture focuses on security attacks, mechanisms,
and services. These can be defined briefly as
•
Security
attack: Any
action that compromises the security of information owned by an
organization.
•
Security
mechanism: A process
(or a device incorporating such a process) that is designed to detect,
prevent, or recover from a security attack.
•
Security
service: A
processing or communication service that enhances the security of the
data processing systems and the information transfers of an organization. The
services are intended to counter security attacks, and they make use of one or
more security mechanisms to provide the service.
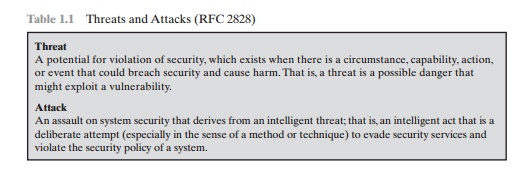
In the literature, the terms threat and attack are
commonly used to mean more or less the same thing. Table 1.1 provides
definitions taken from RFC 2828, Internet Security Glossary.
Related Topics