Chapter: Mobile Networks : Transport and Application Layers
WTA Architecture
WTA Architecture
Browsing
the web using the WML browser is only one application for a handheld device
user. Say a user still wants to make phone calls and access all the features of
the mobile phone network as with a traditional mobile phone. This is where the
wireless telephony application (WTA), the WTA user agent (as shown in Figure),
and the wireless telephony application interface WTAI come in. WTA is a
collection of telephony specific extensions for call and feature control
mechanisms, merging data networks and voice networks.
The WTA
framework integrates advanced telephony services using a consistent user
interface (e.g., the WML browser) and allows network operators to increase
accessibility for various special services in their network. A network operator
can reach more end-devices using WTA because this is integrated in the wireless
application environment (WAE) which handles device-specific characteristics and
environments. WTA should enable third-party developers as well as network
operators to create network-independent content that accesses the basic
features of the bearer network. However, most of the WTA functionality is reserved
for the network operators for security and stability reasons.
WTA
extends the basic WAE application model in several ways:
● Content push: A WTA origin server can push
content, i.e., WML decks or WMLScript, to the client. A push can take place without prior client request. The
content can enable, e.g., the client to handle new network events that were
unknown before.
● Access to telephony functions: The wireless telephony application interface (WTAI, WAP Forum, 2000m) provides many functions to handle telephony events
(call accept, call setup, change of phone book entries etc.).
● Repository for event handlers: The
repository represents a persistent storage on the client for content required to offer WTA
services. Content are either channels or resources. Examples for resources are
WML decks, WMLScript objects, or WBMP pictures. Resources are loaded using WSP
or are pre-installed. A channel comprises references to resources and is
associated with a lifetime. Within this lifetime, it is guaranteed that all resources
the channel points to are locally available in the repository. The motivation
behind the repository is the necessity to react very quickly for time-critical
events (e.g., call accept). It would take too long to load content from a
server for this purpose.
● Security model: Mandatory for WTA is a security
model as many frauds happen with wrong phone
numbers or faked services. WTA allows the client to only connect to trustworthy
gateways, which then have to check if the servers providing content are authorized
to send this content to the client. Obviously, it is not easy to define
trustworthy in this context. In the beginning, the network operator‟s gateway
may be the only trusted gateway and the network operator may decide which
servers are allowed to provide content. Figure 10.30 gives an overview of the
WTA logical architecture.
The
components shown are not all mandatory in this architecture; however, firewalls
or other origin servers may be useful. A minimal configuration could be a
single server from the network operator serving all clients. The client is connected via a mobile
network with a WTA server, other telephone networks (e.g.,
fixed PSTN), and a WAP gateway. A
WML user agent running on the client
or on other user agents is not shown here.
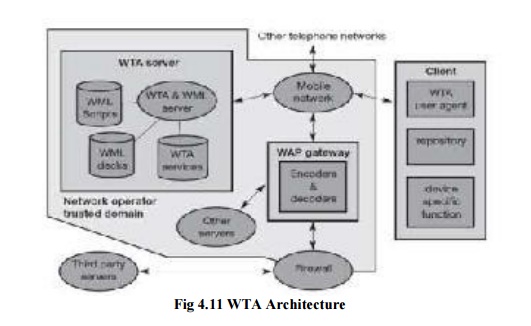
The
client may have voice and data connections over the mobile network. Other
origin servers within the trusted domain may be connected via the WAP gateway.
A firewall is useful to connect third-party origin servers outside the trusted
domain. One difference between WTA servers and other servers besides security
is the tighter control of QoS. A network operator knows (more or less
precisely) the latency, reliability, and capacity of its mobile network and can
have more control over the behavior of the services. Other servers, probably
located in the internet, may not be able to give as good QoS guarantees as the
network operator.
Similarly,
the WTA user agent has a very rigid and real-time context management for
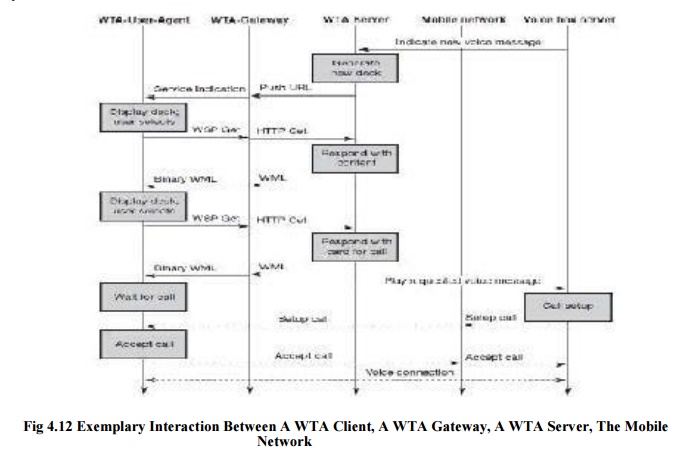
browsing the web compared to the standard WML user agent. Figure shows an
exemplary interaction between a WTA client, a WTA gateway, a WTA server, the
mobile network (with probably many more servers) and a voice box server.
Someone might leave a message on a voice box server as indicated. Without WAP,
the network operator then typically generates an SMS indicating the new message
on the voice box via a little symbol on the mobile phone. However, it is
typically not indicated who left a message, what messages are stored etc. Users
have to call the voice box to check and cannot choose a particular message. In
a WAP scenario, the voice box can induce the WTA server to generate new content
for pushing to the client. An example could be a WML deck containing a list of
callers plus length and priority of the calls. The server does not push this
deck immediately to the client, but sends a push message containing a single
URL to
the client. A short note, e.g., ―5 new calls are stored", could accompany
the push message. The WTA gateway translates the push URL into a service
indication and codes it into a more compact binary format. The WTA user agent
then indicates that new messages are stored. If the user wants to listen to the
stored messages, he or she can request a list of the messages.
This is
done with the help of the URL. A WSP get requests the content the URL points
to. The gateway translates this WSP get into an HTTP get and the server
responds with the prepared list of callers.
After
displaying the content, the user can select a voice message from the list. Each
voice message in this example has an associated URL, which can request a
certain WML card from the server. The purpose of this card is to prepare the
client for an incoming call. As soon as the client receives the card, it waits
for the incoming call. The call is then automatically accepted. The WTA server
also signals the voice box system to set up a (traditional) voice connection to
play the selected voice message. Setting up the call and accepting the call is
shown using dashed lines, as these are standard interactions from the mobile
phone network, which are not controlled by WAP.
Related Topics