Chapter: Mobile Computing : Mobile Internet Protocol and Transport Layer
Key Mechanism in Mobile IP
KEY MECHANISM IN MOBILE IP
The
Mobile IP process has three main phases, which are discussed in the following
sections.
i.Agent Discovery - A
Mobile Node discovers its Foreign and Home Agents during agent
discovery.
ii.Registration - The
Mobile Node registers its current location with the Foreign Agent and Home
Agent during registration.
iii.Tunnelling - A
reciprocal tunnel is set up by the Home Agent to the care-of address (current
location of the Mobile Node on the foreign network) to route packets to the
Mobile Node as it roams.
i.Agent Discovery
During the agent discovery phase, the Home Agent
and Foreign Agent advertise their services on the network by using the ICMP
Router Discovery Protocol (IRDP). The Mobile Node listens to these
advertisements to determine if it is connected to its home network or foreign
network.
The IRDP advertisements carry Mobile IP extensions
that specify whether an agent is a Home Agent, Foreign Agent, or both; its
care-of address; the types of services it will provide such as reverse
tunnelling and generic routing encapsulation (GRE); and the allowed
registration lifetime or roaming period for visiting Mobile Nodes. Rather than
waiting for agent advertisements, a Mobile Node can send out an agent
solicitation. This solicitation forces any agents on the link to immediately
send an agent advertisement.
If a Mobile Node determines that it is connected to
a foreign network, it acquires a care-of address. Two types of care-of
addresses exist:
·
Care-of address acquired from a Foreign Agent
·
Co-located care-of address
A Foreign Agent care-of address is an IP address of
a Foreign Agent that has an interface on the foreign network being visited by a
Mobile Node. A Mobile Node that acquires this type of care-of address can share
the address with other Mobile Nodes. A co-located care-of address is an IP
address temporarily assigned to the interface of the Mobile Node itself.
A
co-located care-of address represents the current position of the Mobile Node
on the foreign network and can be used by only one Mobile Node at a time. When
the Mobile Node hears a Foreign Agent advertisement and detects that it has
moved outside of its home network, it begins registration.
ii.Registration
The
Mobile Node is configured with the IP address and mobility security association
(which includes the shared key) of its Home Agent. In addition, the Mobile Node
is configured with either its home IP address, or another user identifier, such
as a Network Access Identifier.
The
Mobile Node uses this information along with the information that it learns
from the Foreign Agent advertisements to form a Mobile IP registration request.
It adds the registration request to its pending list and sends the registration
request to its Home Agent either through the Foreign Agent or directly if it is
using a co-located care-of address and is not required to register through the
Foreign Agent.
If the
registration request is sent through the Foreign Agent, the Foreign Agent
checks the validity of the registration request, which includes checking that
the requested lifetime does not exceed its limitations, the requested tunnel
encapsulation is available, and that reverse tunnel is supported. If the
registration request is valid, the Foreign Agent adds the visiting Mobile Node
to its pending list before relaying the request to the Home Agent. If the
registration request is not valid, the Foreign Agent sends a registration reply
with appropriate error code to the Mobile Node.
The Home
Agent checks the validity of the registration request, which includes authentication
of the Mobile Node. If the registration request is valid, the Home Agent
creates a mobility binding (an association of the Mobile Node with its care-of
address), a tunnel to the care-of address, and a routing entry for forwarding
packets to the home address through the tunnel.
The Home
Agent then sends a registration reply to the Mobile Node through the Foreign
Agent (if the registration request was received via the Foreign Agent) or
directly to the Mobile Node. If the registration request is not valid, the Home
Agent rejects the request by sending a registration reply with an appropriate
error code.
The
Foreign Agent checks the validity of the registration reply, including ensuring
that an associated registration request exists in its pending list. If the
registration reply is valid, the Foreign Agent adds the Mobile Node to its
visitor list, establishes a tunnel to the Home Agent, and creates a routing
entry for forwarding packets to the home address. It then relays the
registration reply to the Mobile Node.
Finally,
the Mobile Node checks the validity of the registration reply, which includes
ensuring an associated request is in its pending list as well as proper
authentication of the Home Agent. If the registration reply is not valid, the
Mobile Node discards the reply. If a valid registration reply specifies that
the registration is accepted, the Mobile Node is confirmed that the mobility
agents are aware of its roaming. In the co-located care-of address case, it
adds a tunnel to the Home Agent. Subsequently, it sends all packets to the
Foreign Agent.
The
Mobile Node reregisters before its registration lifetime expires. The Home
Agent and Foreign Agent update their mobility binding and visitor entry,
respectively, during re-registration. In the case where the registration is
denied, the Mobile Node makes the necessary adjustments and attempts to
register again. For example, if the registration is denied because of time
mismatch and the Home Agent sends back its time stamp for synchronization, the Mobile
Node adjusts the time stamp in future registration requests.
Thus, a
successful Mobile IP registration sets up the routing mechanism for
transporting packets to and from the Mobile Node as it roams.
iii.Tunnelling
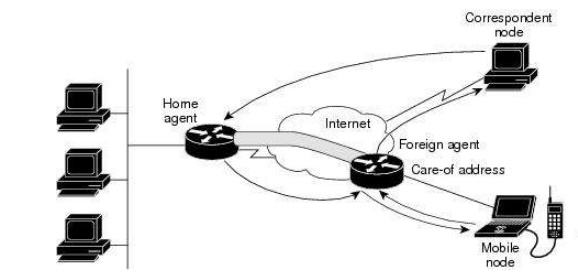
The
Mobile Node sends packets using its home IP address, effectively maintaining
the appearance that it is always on its home network. Even while the Mobile
Node is roaming on foreign networks, its movements are transparent to
correspondent nodes.Data packets addressed to the Mobile Node are routed to its
home network, where the Home Agent now intercepts and tunnels them to the
care-of address toward the Mobile Node. Tunnelling has two primary functions:
encapsulation of the data packet to reach the tunnel endpoint, and
decapsulation when the packet is delivered at that endpoint. The default tunnel
mode is IP Encapsulation within IP Encapsulation. Optionally, GRE and minimal
encapsulation within IP may be used.Typically, the Mobile Node sends packets to
the Foreign Agent, which routes them to their final destination, the
Correspondent Node, as shown in Figure 2.
Packet Forwarding
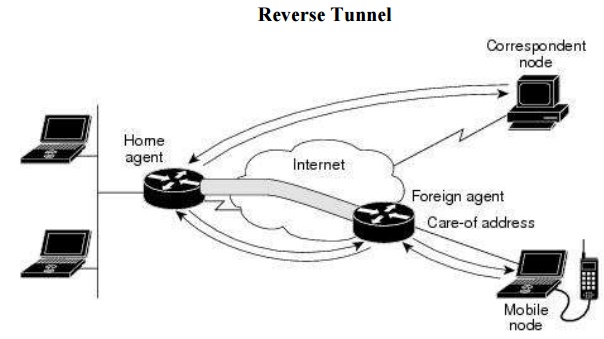
However,
this data path is topologically incorrect because it does not reflect the true
IP network source for the data — rather, it reflects the home network of the
Mobile Node. Because the packets show the home network as their source inside a
foreign network, an access control list on routers in the network called
ingress filtering drops the packets instead of forwarding them. A feature
called reverse tunnelling solves this problem by having the Foreign Agent
tunnel packets back to the Home Agent when it receives them from the Mobile
Node.
Reverse Tunnel
Tunnel
MTU discovery is a mechanism for a tunnel encapsulator such as the Home Agent
to participate in path MTU discovery to avoid any packet fragmentation in the
routing path between a Correspondent Node and Mobile Node. For packets destined
to the Mobile Node, the Home Agent maintains the MTU of the tunnel to the
care-of address and informs the Correspondent Node of the reduced packet size.
This improves routing efficiency by avoiding fragmentation and reassembly at
the tunnel endpoints to ensure that packets reach the Mobile Node.
Security
Mobile IP
uses a strong authentication scheme for security purposes. All registration
messages between a Mobile Node and Home Agent are required to contain the
Mobile-Home Authentication Extension (MHAE).
The
integrity of the registration messages is protected by a preshared 128-bit key
between a Mobile Node and Home Agent. The keyed message digest algorithm 5
(MD5) in "prefix+suffix" mode is used to compute the authenticator
value in the appended MHAE, which is mandatory. Mobile IP also supports the
hash-based message authentication code (HMAC-MD5). The receiver compares the
authenticator value it computes over the message with the value in the
extension to verify the authenticity.
Optionally,
the Mobile-Foreign Authentication Extension and Foreign-Home Authentication
Extension are appended to protect message exchanges between a Mobile Node and
Foreign Agent and between a Foreign Agent and Home Agent, respectively.
Replay
protection uses the identification field in the registration messages as a
timestamp and sequence number. The Home Agent returns its time stamp to
synchronize the Mobile Node for registration.
Cisco IOS
software allows the mobility keys to be stored on an authentication,
authorization, and accounting (AAA) server that can be accessed using TACACS+
or RADIUS protocols. Mobile IP in Cisco IOS software also contains registration
filters, enabling companies to restrict who is allowed to register.
Related Topics