Chapter: Information Security : Logical Design
Contingency Planning (CP)
CONTINGENCY PLANNING (CP)
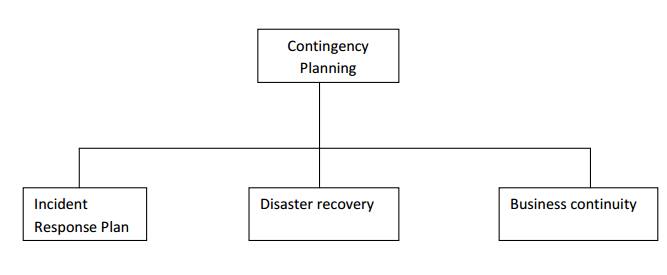
ü Contingency
Planning (CP) comprises a set of plans designed to ensure the effective
reaction and recovery from an attack and the subsequent restoration to normal
modes of business operations.
ü Organizations
need to develop disaster recovery plans, incident response plans, and business
continuity plans as subsets of an overall CP.
ü An incident response plan (IRP) deals with
the identification, classification, response, and recovery from an incident,
but if the attack is disastrous(e.g., fire, flood, earthquake) the process moves
on to disaster recovery and BCP
ü A disaster recovery plan (DRP) deals with
the preparation for and recovery from a disaster, whether natural or man-made
and it is closely associated with BCP.
ü A Business continuity plan (BCP) ensures
that critical business functions continue, if a catastrophic incident or
disaster occurs. BCP occurs concurrently with DRP when the damage is major or
long term, requiring more than simple restoration of information and
information resources.
1 Components of Contingency Planning
There are
six steps to contingency planning. They are
· Identifying
the mission-or business-critical functions,
· Identifying
the resources that support the critical functions,
· Anticipating
potential contingencies or disasters,
· Selecting
contingency planning strategies,
· Implementing
the contingencies strategies,
· and
Testing and revising the strategy.
2 Business Impact Analysis (BIA)
ü A BIA is
an investigation and assessment of the impact that various attacks can have on
the organization.
ü The
contingency planning team conducts the BIA in the following stages,
1 Threat
attack indentification and prioritization
2 Business
unit analysis
3 Attack
success scenario development
4 Potential
damage assessment
5 Subordinate
plan classification
3 Incident response plan (IRP)
ü It is the
set of activities taken to plan for, detect, and correct the impact of an
incident on information assets.
ü IRP
consists of the following 4 phases:
1 Incident
Planning
2 Incident
Detection
3 Incident
Reaction
4 Incident
Recovery
Incident Planning
ü Planning
for an incident is the first step in the overall process of incident response
planning.
ü The
planners should develop a set of documents that guide the actions of each
involved individual who reacts to and recovers from the incident.
ü These
plans must be properly organized and stored to be available when and where
needed, and in a useful format.
Incident Detection
ü Incident
Detection relies on either a human or automated system, which is often the help
desk staff, to identify an unusual occurrence and to classify it properly as an
incident.
ü The
mechanisms that could potentially detect an incident include intrusion
detection systems (both host-based and network based), virus detection
software, systems administrators, and even end users.
ü Once an
attack is properly identified, the organization can effectively execute the
corresponding procedures from the IR plan. Thus, incident classification is the process of examining a potential
incident, or incident candidate, and
determining whether or not the candidate constitutes an actual incident.
ü Incident Indicators- There
is a number of occurrences that could signal the presence of an incident candidate.
ü Donald Pipkin, an IT security expert,
identifies three categories of incident indicators:
Possible, Probable, and Definite Indicators.
ü Possible Indicators- There
are 4 types of possible indicators of events ,they are,
- Presence
of unfamiliar files.
- Presence
or execution of unknown programs or processes.
Unusual consumption of computing resources
Unusual system crashes
ü Probable Indicators- The
four types of probable indicators of incidents are
- Activities
at unexpected times.
- Presence
of new accounts
- Reported
attacks
- Notification
from IDS
ü Definite Indicators- The five
types of definite indicators of incidents are
-
Use of Dormant accounts
-
Changes to logs
ü Presence
of hacker tools
ü Notifications
by partner or peer
ü Notification
by hacker
· It
consists of actions outlined in the IRP that guide the organization in
attempting to stop the incident, mitigate the impact of the incident, and
provide information for recovery from the incident.
· These
actions take place as soon as the incident itself is over.
· In
reacting to the incident there are a number of actions that must occur quickly,
including notification of key personnel and documentation of the incident.
· These
must have been prioritized and documented in the IRP for quick use in the heat
of the moment.
Incident Recovery
The
recovery process involves much more than the simple restoration of stolen,
damaged, or destroyed data files. It involves the following steps.
Identify
the Vulnerabilities
Address
the safeguards.
Evaluate
monitoring capabilities
Restore
the data from backups.
Restore
the services and processes in use.
Continuously
monitor the system
Restore the confidence of the members of the organization’s communities of interest.
Disaster Recovery Plan (DRP)
DRP
provides detailed guidance in the event of a disaster and also provides details
on the roles and responsibilities of the various individuals involved in the
disaster recovery effort, and identifies the personnel and agencies that must
be notified.
At a
minimum, the DRP must be reviewed during a walk-through or talk-through on a
periodic basis.
Many of
the same precepts of incident response apply to disaster recovery:
here must
be a clear establishment of priorities
There
must be a clear delegation of roles and responsibilities
Someone
must initiate the alert roster and notify key personnel.
Someone
must be tasked with the documentation of the disaster.
If and
only if it is possible, attempts must be made to mitigate the impact of the
disaster on the operations of the organization.
Business Continuity Plan (BCP)
It prepares
an organization to reestablish critical business operations during a disaster
that affects operations at the primary site.
If a
disaster has rendered the current location unusable for continued operations,
there must be a plan to allow the business to continue to function.
Developing Continuity Programs
Once the
incident response plans and disaster recovery plans are in place, the
organization needs to consider finding temporary facilities to support the
continued viability of the business in the event of a disaster.
The
development of the BCP is simpler than that of the IRP and DRP ,in that it
consists of selecting a continuity strategy and integrating the off-site data
storage and recovery functions into this strategy.
Continuity Strategies
There are
a number of strategies from which an organization can choose when planning for
business continuity.
The
determining factor in selection between these options is usually cost.
In
general there are three exclusive options: Hot sites, Warm Sites, and Cold
sites; and three shared functions: Time-share, Service bureaus, and Mutual
Agreements.
Hot sites: A hot site is a fully
configured facility, with all services, communications links, and physical plant operations
including heating and air conditioning. It is the pinnacle of contingency
planning, a duplicate facility that needs only the latest data backups and the
personnel to function as a fully operational twin of the original.
Disadvantages include the need to provide maintenance for all the systems and
equipment in the hot site, as well as physical and information security.
Warm sites: A warm site includes computing
equipment and peripherals with servers but not client work stations. It has many of the advantages of a hot site,
but at a lower cost.
Cold Sites: A cold site provides only
rudimentary services and facilities, No computer hardware or peripherals are provided. Basically a cold site is an
empty room with heating, air conditioning, and electricity. The main advantage
of cold site is in the area of cost.
Time-shares: It allows the organization to
maintain a disaster recovery and business
continuity option, but at a reduced overall cost. The advantages are
identical to the type of site selected(hot, warm, or cold). The disadvantages
are the possibility that more than one organization involved in the time share
may need the facility simultaneously and the need to stock the facility with
the equipment and data from all organizations involved, the negotiations for
arranging the time-share, and associated arrangements, should one or more
parties decide to cancel the agreement or to sublease its options.
Service bureaus: A service bureau is an agency
that provides a service for a fee. In the case of disaster recovery and continuity planning, the service is the
agreement to provide physical facilities in the event of a disaster. These
types of agencies also provide off-site data storage for a fee. The
disadvantage is that it is a service, and must be renegotiated periodically.
Also, using a service bureau can be quite expensive.
Mutual Agreements: A mutual
agreement is a contract between two or more organizations that specifies how each will assist the other in the event of a
disaster.
Related Topics