Chapter: Fundamentals of Database Systems : Transaction Processing, Concurrency Control, and Recovery : Database Recovery Techniques
Recovery Techniques Based on Immediate Update
Recovery Techniques Based on Immediate Update
In these techniques, when a transaction issues an update command, the
database on disk can be updated immediately,
without any need to wait for the transaction to reach its commit point. Notice
that it is not a requirement that
every update be
applied immediately to disk; it is just possible that some updates are
applied to disk before the transaction
commits.
Provisions must be made for undoing
the effect of update operations that have been applied to the database by a failed transaction. This is accomplished
by rolling back the transaction and undoing the effect of the transaction’s write_item operations. Therefore, the UNDO-type log entries, which include the old value (BFIM) of the item, must be
stored in the log. Because UNDO can be needed during recovery,
these methods follow a steal strategy
for deciding when updated main memory buffers can be written back to disk (see
Section 23.1.3). Theoretically, we can distinguish two main categories of
immediate update algorithms. If the recovery technique ensures that all updates
of a transaction are recorded in the database on disk before the transaction
commits, there is never a need to REDO any operations of committed transactions.
This is called the UNDO/NO-REDO recovery algorithm. In this method, all updates by a transaction
must be recorded on disk before the
transaction commits, so that REDO is never needed. Hence, this
method must utilize the force strategy for deciding when
updated main memory buffers are written back to disk (see Section 23.1.3).
If the transaction is allowed to commit before all its changes are
written to the data-base, we have the most general case, known as the UNDO/REDO recovery algorithm. In this
case, the steal/no-force strategy is
applied (see Section 23.1.3). This is also
the most complex technique. We will outline an UNDO/REDO recovery
algo-rithm and leave it as an exercise for the reader to develop the UNDO/NO-REDO vari-ation. In Section 23.5, we describe a more practical approach
known as the ARIES recovery technique.
When concurrent execution is permitted, the recovery process again
depends on the protocols used for concurrency control. The procedure RIU_M (Recovery using Immediate Updates for a Multiuser environment) outlines
a recovery algorithm for concurrent transactions with immediate update (UNDO/REDO recovery). Assume that the log includes checkpoints and that the
concurrency control protocol pro-duces strict
schedules—as, for example, the strict two-phase locking protocol does.
Recall that a strict schedule does not allow a transaction to read or write an
item unless the transaction that last wrote the item has committed (or aborted
and rolled back). However, deadlocks can occur in strict two-phase locking,
thus requiring abort and UNDO of transactions. For a strict
schedule, UNDO of an operation requires changing the item back to its old value (BFIM).
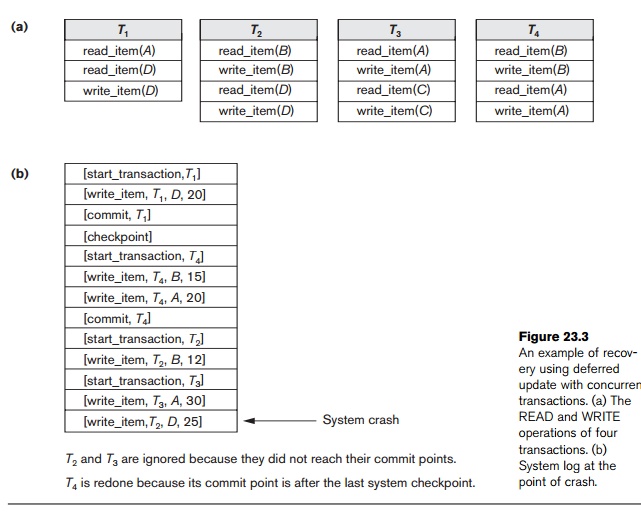
Procedure RIU_M (UNDO/REDO with checkpoints).
1. Use two lists of transactions maintained by the system: the committed trans-actions since the last checkpoint and the active transactions.
2. Undo all the write_item operations of the active (uncommitted) transactions, using the UNDO procedure. The operations should be undone in the reverse of the order in which they were written into the log.
3. Redo all the write_item operations of the committed transactions from the log, in the order in which they were written into the log, using the REDO procedure defined earlier.
The UNDO procedure is defined as follows:
Procedure UNDO (WRITE_OP). Undoing a write_item operation write_op consists of examining its log entry [write_item, T, X, old_value, new_value] and set-ting the value of item X
in the database to old_value, which is the before image
(BFIM). Undoing a number of write_item operations from one or more
trans-actions from the log must proceed in the reverse order from the order in which the operations were written
in the log.
As we discussed for the NO-UNDO/REDO procedure, step 3 is more
efficiently done by starting from the end
of the log and redoing only the last
update of each item X.
Whenever an item is redone, it is added to a list of redone items and is
not redone again. A similar procedure can be devised to improve the efficiency
of step 2 so that an item can be undone at most once during recovery. In this
case, the earliest UNDO is applied first by scanning the
log in the forward direction (starting from the beginning of the log). Whenever
an item is undone, it is added to a list of undone items and is not undone
again.
Related Topics