Chapter: Cryptography and Network Security Principles and Practice : Overview
Security Services
SECURITY
SERVICES
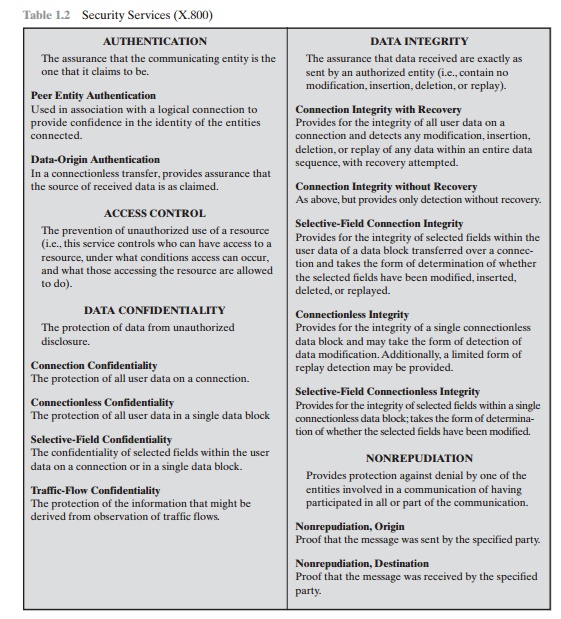
X.800
defines a security service as a service that is provided by a protocol layer of
communicating open systems and that ensures adequate security of the systems or
of data transfers. Perhaps a clearer definition is found in RFC 2828, which
provides the following definition: a processing or communication service that
is provided by
a system
to give a specific kind of protection to system resources; security services
implement security policies and are implemented by security mechanisms.
X.800
divides these services into five categories and fourteen specific services
(Table 1.2). We look at each category in turn.
Authentication
The authentication service is concerned with assuring that a
communication is authentic. In the case of a single message, such as a warning
or alarm signal, the function of the authentication service is to assure the
recipient that the message is from the source that it claims to be from. In the
case of an ongoing interaction, such as the connection of a terminal to a host,
two aspects are involved. First, at the time of connection initiation, the
service assures that the two entities are authentic, that is, that each is the
entity that it claims to be. Second, the service must assure that the
connection is not interfered with in such a way that a third party can
masquerade as one of the two legitimate parties for the purposes of
unauthorized transmission or reception.
Two
specific authentication services are defined in X.800:
•
Peer
entity authentication: Provides
for the corroboration of the identity of a peer entity in an
association. Two entities are considered peers if they implement to same
protocol in different systems; e.g., two TCP mod-ules in two communicating
systems. Peer entity authentication is provided for use at the establishment
of, or at times during the data transfer phase of, a connection. It attempts to
provide confidence that an entity is not performing either a masquerade or an
unauthorized replay of a previous connection.
•
Data
origin authentication: Provides
for the corroboration of the source of a data unit. It does not provide
protection against the duplication or modification of data units. This type of
service supports applications like electronic mail, where there are no prior
interactions between the commu-nicating entities.
Access
Control
In the context of network security, access control is the
ability to limit and control the access to host systems and applications via
communications links. To achieve this, each entity trying to gain access must
first be identified, or authenticated, so that access rights can be tailored to
the individual.
Data
Confidentiality
Confidentiality is the protection of transmitted data from
passive attacks. With respect to the content of a data transmission, several
levels of protection can be identified. The broadest service protects all user
data transmitted between two users over a period of time. For example, when a
TCP connection is set up between two systems, this broad protection prevents
the release of any user data transmitted over the TCP connection. Narrower
forms of this service can also be defined, including the protection of a single
message or even specific fields within a message. These refinements are less
useful than the broad approach and may even be more complex and expensive to
implement.
The other
aspect of confidentiality is the protection of traffic flow from analysis.
This requires that an attacker not be able to observe the source
and destination, frequency, length, or other characteristics of the traffic on
a communications facility.
Data
Integrity
As with confidentiality, integrity can apply to a stream of messages,
a single message, or selected fields within a message. Again, the most useful
and straightforward approach is total stream protection.
A connection-oriented integrity service, one that deals with a
stream of messages, assures that messages are received as sent with no
duplication, inser-tion, modification, reordering, or replays. The destruction
of data is also covered under this service. Thus, the connection-oriented
integrity service addresses both message stream modification and denial of service.
On the other hand, a connec-tionless integrity service, one that deals with
individual messages without regard to any larger context, generally provides
protection against message modification only.
We can make a distinction between service with and without
recovery. Because the integrity service relates to active attacks, we are
concerned with detection rather than prevention. If a violation of integrity is
detected, then the service may simply report this violation, and some other
portion of software or human intervention is required to recover from the
violation. Alternatively, there are mechanisms available to recover from the
loss of integrity of data, as we will review subsequently. The incorporation of
automated recovery mechanisms is, in general, the more attractive alternative.
Nonrepudiation
Nonrepudiation prevents either sender or receiver from denying a
transmitted message. Thus, when a message is sent, the receiver can prove that
the alleged sender in fact sent the message. Similarly, when a message is
received, the sender can prove that the alleged receiver in fact received the
message.
Availability
Service
Both X.800 and RFC 2828 define availability to be the property
of a system or a system resource being accessible and usable upon demand by an
authorized system entity, according to performance specifications for the
system (i.e., a system is available if it provides services according to the
system design whenever users request them). A variety of attacks can result in
the loss of or reduction in availability. Some of these attacks are amenable to
automated countermeasures, such as authentication and encryption, whereas
others require some sort of physical action to prevent or recover from loss of
availability of elements of a distributed system.
X.800 treats availability as a property to be associated with
various security services. However, it makes sense to call out specifically an
availability service. An availability service is one that protects a system to
ensure its availability. This service addresses the security concerns raised by
denial-of-service attacks. It depends on proper management and control of
system resources and thus depends on access control service and other security
services.
Related Topics